Table of Contents
Security teams are not short on tools. They are short on reliable signals.
Enterprise networks generate huge amounts of telemetry data every second. The telemetry data that is generated within an enterprise network includes packets, flows, DNS activity logs, failed login attempts and encrypted connections to the internet. Within this stream of data are early indications of compromise. The challenge is to identify these early indications of compromise before any harm can be done.
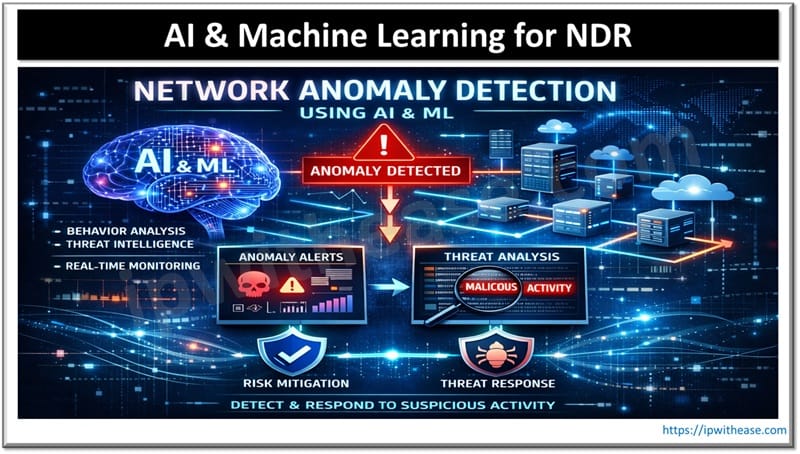
The role of NDR (Network Detection and Response) with the aid of machine learning is essential in this process.
In this article, we discuss key NDR concepts for security leaders and how NDR fits into a modern cyber defense strategy by using AI to detect abnormal activity on the network.
What is Network Anomaly Detection?
Network anomaly detection (NDR) involves recognizing actions that differ from a defined norm of typical network operations.
Traditional detection mechanisms rely on:
- Signatures
- Known indicators of compromise
- Predefined correlation rules
These methods work well against known threats. They struggle against:
- Zero-day attacks
- Insider misuse
- Credential abuse
- Encrypted command-and-control channels
Solutions for NDR (Network Detection and Response) are designed to monitor a network activity on a real time basis and develop a baseline for user activity, device activity and segment activity. In the event that there is a notable change in the activity on the network from the baseline, that activity will be flagged for review. Abnormal behaviors are the basis of detection as opposed to just known threat patterns.
Why are Signature-Based Systems no Longer Enough?
Attackers have adapted.
Modern adversaries:
- Use legitimate administrative tools
- Move laterally in small, quiet steps
- Operate within encrypted sessions
- Blend into routine traffic
A signature cannot detect what it has never seen. A static rule cannot anticipate every variation of misuse.
Machine learning addresses this gap by modeling:
- Typical communication paths
- Expected data volumes
- Normal login patterns
- Peer group behavior
When a finance user suddenly initiates unusual east-west traffic or accesses systems outside their historical pattern, that deviation becomes visible.
The alert is generated because the behavior is statistically inconsistent, not because it matches a known malware hash.
How Does Machine Learning Operate Inside NDR?
Let’s focus on what actually matters.
1. Behavioral Baselining
Most NDR platforms use unsupervised learning techniques to establish a baseline of network behavior without needing labeled attack data.
They analyze:
- Flow metadata
- Session durations
- Protocol distribution
- Device-to-device communication patterns
Over time, the system builds an evolving model of what “normal” looks like for each asset and user group.
When activity falls outside expected thresholds, it is scored for risk.
2. Classification of Known Threat Behaviors
Supervised models are trained on historical attack data to recognize:
- Beaconing patterns
- Lateral movement sequences
- Known exfiltration behaviors
This strengthens detection precision while behavioral models continue to identify novel patterns.
3. Encrypted Traffic Analysis
With most enterprise traffic encrypted, visibility cannot rely on payload inspection alone.
NDR systems analyze:
- TLS handshake characteristics
- Flow timing patterns
- Packet size distribution
- Certificate reuse anomalies
This allows identification of suspicious encrypted sessions without decrypting content, maintaining compliance while improving detection coverage.
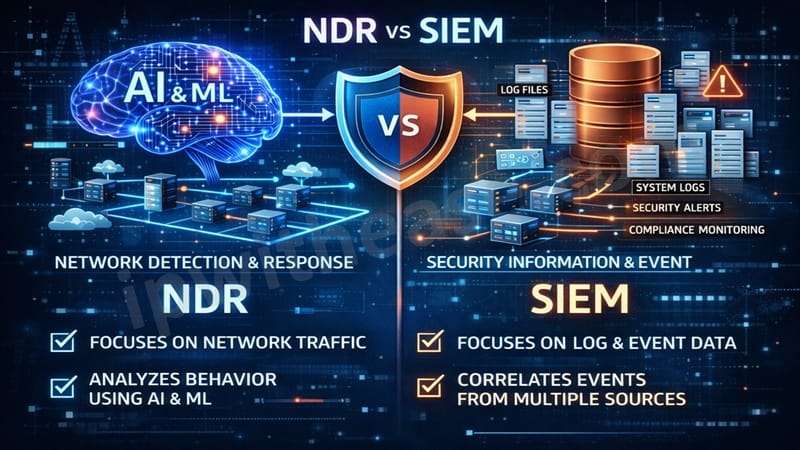
How is NDR Different from SIEM?
SIEM platforms aggregate and correlate logs. They are essential components of security architecture.
However, they depend on:
- Log completeness
- Accurate parsing
- Well-maintained correlation rules
NDR works directly from network telemetry. It observes what devices actually do on the wire.
Here is the practical difference:
| SIEM | NDR |
|---|---|
| Log-driven | Network-telemetry driven |
| Rule-based correlation | Behavioral analytics |
| Strong for compliance and log retention | Strong for lateral movement and anomaly detection |
| Detects known patterns well | Detects both known and unknown behaviors |
Used together, they create layered visibility. Used independently, blind spots remain.
How does NDR Reduce Alert Fatigue?
One of the biggest operational challenges in a SOC is the volume.
Machine learning improves efficiency by:
- Clustering related anomalies
- Assigning contextual risk scores
- Building event timelines
- Mapping likely attack paths
Instead of hundreds of isolated alerts, analysts receive consolidated incident views.
In real-world deployments, this reduces investigation time and improves confidence in triage decisions. The value is not just in detection, it is in prioritization.
Can Machine Learning Introduce New Risks?
Yes, if implemented poorly. Three considerations matter:
Model Drift
Networks change. Baselines must adapt without learning malicious activity as normal behavior.
Explainability
Analysts must understand why something was flagged. Mature NDR platforms provide transparency into triggering features and deviations.
Tuning
Initial deployment requires calibration. Without proper thresholds and segmentation, false positives can erode trust.
When properly managed, these challenges are operational, not structural.
How does NDR Identify Insider Threats?
Insider activity often looks legitimate at first glance. But it frequently breaks behavioral norms.
Examples:
- A developer accessing HR systems
- An employee gradually increases data transfers over weeks
- Unusual login patterns outside peer group behavior
Machine learning identifies:
- Deviations from peer baselines
- Abnormal data access frequency
- Rare cross-segment communications
These anomalies, when correlated, form early indicators of risk.
Why is Encrypted Traffic Visibility Critical?
Encrypted traffic now dominates enterprise environments. Attackers use this to their advantage.
Without network-level behavioral monitoring, malicious command-and-control traffic can remain hidden for extended periods.
NDR provides visibility through:
- Traffic metadata analysis
- Behavioral pattern recognition
- Flow anomaly detection
This reduces reliance on full decryption while preserving detection capability.
How Should Organizations Approach NDR Adoption?
Implementation should be deliberate. Best practices include:
- Ensuring full east-west visibility across internal segments.
- Integrating NDR outputs into existing incident response workflows.
- Establishing feedback loops between analysts and detection models.
- Periodically validating detection performance.
NDR should strengthen operational processes, not operate in isolation.
Why does This Matter Strategically?
Threat actors continue refining stealth techniques. Defensive systems must identify what traditional tools overlook. Network Detection and Response (NDR) provides:
- Early lateral movement detection
- Visibility into encrypted sessions
- Behavioral anomaly identification
- Faster incident scoping
For organizations serious about strengthening detection maturity, behavioral network analytics is no longer optional.
The future of network security does not rely on larger rule sets. It relies on understanding how your network behaves and recognizes when it doesn’t.
That is where NDR delivers measurable value.
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.