Table of Contents
Most firms employ office networks, remote endpoints, cloud platforms, SaaS tools, and evolving dispersed workloads. But in these cases, security teams need more than one control point. Threat prevention involves understanding how dangers cross systems, identities, devices, and applications.
That’s why more teams prioritize cybersecurity threat prevention above isolated controls. Unmanaged devices, poorly secured workloads, and weak identification procedures can compromise a company’s strong network defenses. The teamwork between these levels, not their individual performance, determines the effectiveness of prevention.

IBM has warned that the growing interdependence between cloud, SaaS, and identity systems has become a primary driver of cyber risk. The IBM X‑Force Threat Intelligence Index 2026 reported a near-fourfold increase on supply chain and ecosystem‑level attacks. Open‑source components, integrations, and administrative platforms are increasingly targeted, rather than core infrastructure.
Network Security Matters, but it’s Not Everything
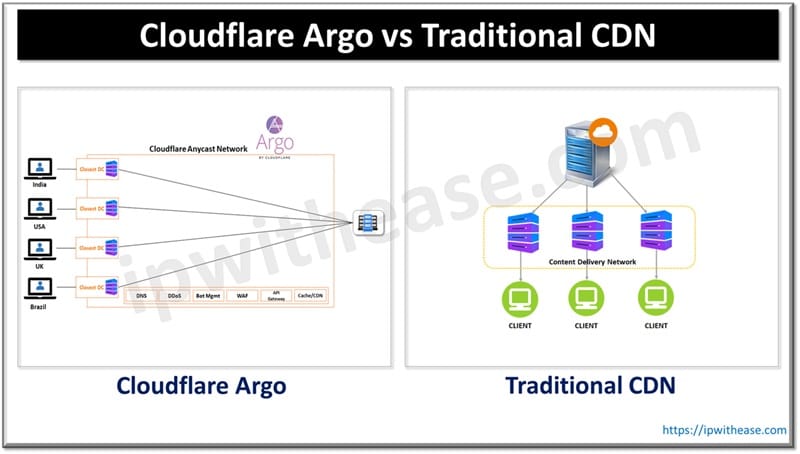
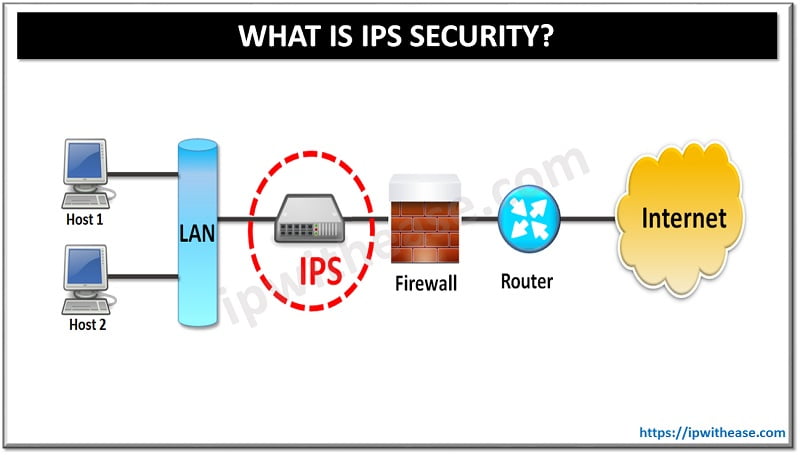
Enterprise defense depends on the network. Firewalls, intrusion prevention, segmentation, DNS limitations, and traffic inspection reduce exposure and block known hostile actions. These measures underpinned preventative strategies for decades and still matter.
Their environment has altered. Users connect, and apps run across multiple locations, so business traffic no longer flows through a single perimeter. A good preventive plan has strong network controls but recognizes that threats can cross borders. Prevention must now account for endpoint behavior, identity abuse, and cloud workloads without relying on outdated network assumptions.
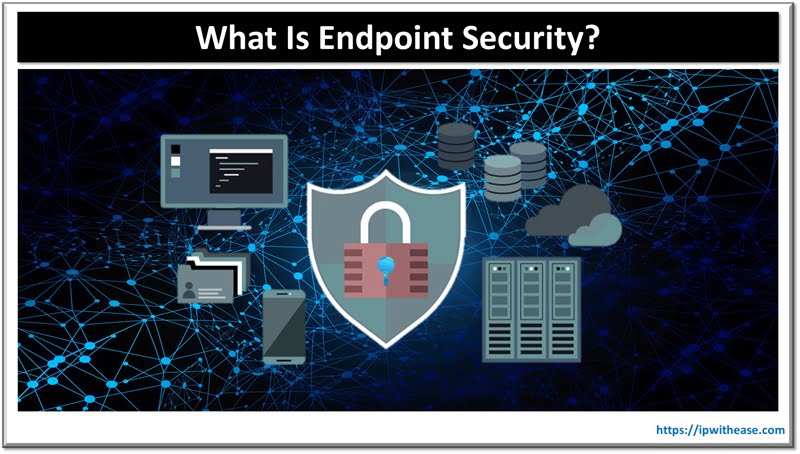
Endpoints Pose Considerable Risks
Prevention works or fails on laptops, mobile devices, and employee workstations. These systems manage email, downloads, browser sessions, collaboration, local apps, and remote access.
A practical strategy depends on behavioral detection, application control, consistent patching, device visibility, and minimizing misuse or compromise. Rather than focusing only on detecting suspicious activity, effective prevention reduces the underlying conditions that make endpoints easier to attack.
New Exposure from Cloud Workloads
Cloud workloads can become exposed if visibility and control are weak, making them accessible to unauthorized users.
IBM’s research shows that misconfigured identity connectors, exposed credentials, and weak cross‑platform governance allow attackers to pivot laterally through trusted systems.
Early 2026 Incidents Highlighted Containment Failures
Early this year, actors like Zestix exploited stolen credentials in cloud-sharing platforms, exposing corporate data from healthcare, defense, and government sectors. Meanwhile ShinyHunters’ breach of Crunchbase (2 million records) and SoundCloud (almost 30 million accounts) relied on social engineering and phishing. These incidents showed us yet again that attackers blend into trusted workflows via identity abuse and misconfigurations. The need for integrated XDR, least-privilege enforcement, and company-wide playbooks is clear.
Operationalizing Threat Prevention
Even with strong policies and layered defenses, prevention depends on how organizations translate security insight into action. Signals from networks, endpoints, and cloud workloads often exist, but without correlation and timely response, they lose impact.
Modern security operations use automation, analytics, and orchestration to manage this complexity. Machine learning‑based detection systems can flag unusual behaviors across multiple domains (such as anomalous login locations linked with endpoint data exfiltration).
Security information and event management (SIEM) and extended detection and response (XDR) platforms help connect these signals, allowing analysts to prioritize alerts that truly indicate risk rather than routine fluctuation.
It’s also important that teams collaborate. Network, infrastructure, identity, and cloud specialists must share a unified view of assets, configurations, and user behavior. Clear playbooks for prevention events (unauthorized access, privilege escalation, misconfiguration) allow for quicker containment before a compromise spreads.
Last Words
If 2026 is going to be a better year for security teams than 2025, leaders must move away from siloed defenses to unified visibility across networks, endpoints, cloud workloads, and identity layers. Each integration and credential must be treated as a potential pivot point.
FAQs: Threat Prevention Essentials
Q.1 Why is unified monitoring important?
Attackers move across systems, and unified monitoring helps identify patterns missed by isolated tools.
Q.2 Are firewalls still important in 2026?
Yes, but they should work alongside endpoint, identity, and cloud controls for full coverage.
Q.3 What role does identity play in prevention?
Compromised credentials are prime attack vectors. Strong governance and least‑privilege access are essential.
Q.4 How can teams operationalize prevention?
By connecting their insights and acting quickly together. Platforms like SIEM and XDR turn scattered data into meaningful insights. Automation can take care of routine tasks, giving analysts more time to focus on complex threats and high‑impact decisions.
Most importantly, network, cloud, and endpoint teams should work from shared playbooks that encourage collaboration and consistent response instead of isolated action.
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.