Table of Contents
The internet has a problem called BGP hijacking. This is also known as prefix hijacking. It is a serious issue with the way the internet works. BGP hijacking is when a malicious (or misconfigured) network falsely announces ownership of IP address prefixes it doesn’t actually control, causing internet traffic to be misrouted through that network.
When one network tells another network a route the other network just accepts it without checking if it is true.
Causes of BGP Hijacking
BGP hijacking can be broadly categorized based on its intent.
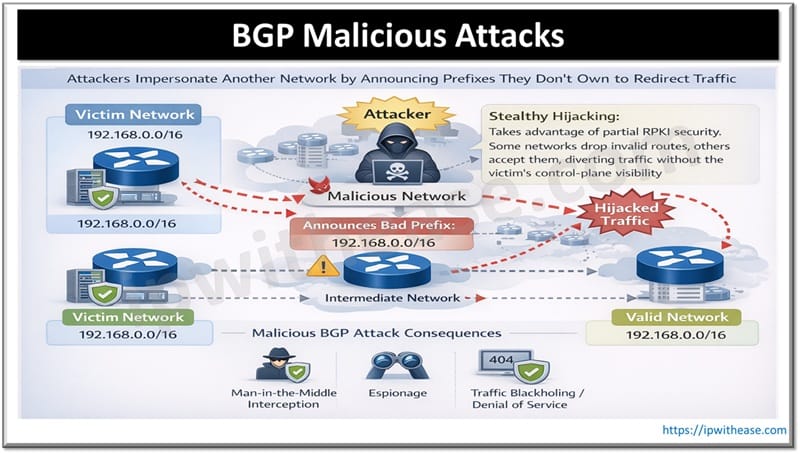
Malicious Attacks
These are deliberate acts to impersonate another network. Attackers announce prefixes they do not own. This is done to redirect traffic. The goal is often to intercept traffic. It can also be used for espionage. Another goal is to blackhole traffic. This causes a denial of service.
A sophisticated variant is called hijacking. It exploits the deployment of security measures, like RPKI. In this case some networks drop the route. Others unknowingly accept it. This allows traffic to be diverted. The victim does not have control-plane visibility.
Accidental Misconfigurations
Sometimes people make mistakes when they set up their network. This can happen when someone does something or when the router is not set up correctly. When this happens the network can start sending out information that it should not be sending out. This can be very bad for the network like when someone is trying to hurt it on purpose.
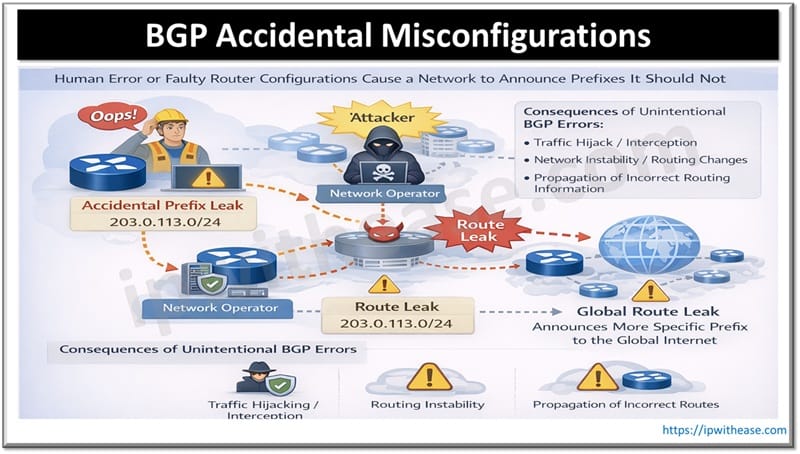
For example, someone who takes care of a network might accidentally tell the networks that they are connected to about a specific group of addresses that they learned from one of their customers. This can cause problems around the world because it can make it seem like the network is supposed to be in charge of those addresses when really it is not. Accidental misconfigurations like this can be just as bad as when someone’s trying to cause trouble on purpose. Network operators have to be careful to avoid misconfigurations and make sure that their network is set up correctly to prevent problems, like this from happening.
Real World Examples
Several big incidents show how BGP hijacking can cause problems:
June 2025 DNS Root Server Attack
Someone sent internet routes for some important DNS root servers. This happened for 90 minutes. It could have let them control what websites people in some areas saw which could have led to them getting peoples data. The DNS Root Servers are important. They help turn website names into addresses that computers can understand.
In this case the attack could have allowed hackers to intercept data. They could have seen what people were looking at online. Even stolen peoples’ information. BGP hijacking is a deal. It can let hackers control internet traffic. They can send people to websites. Intercept people’s data. It is easy to see why BGP hijacking is bad. It is harder to stop. That is why incidents, like the June 2025 DNS Root Server Attack are concerning.
Cloudflare 1.1.1.1 had a problem on June 27 2024
Something bad happened with the internet routes. This was because of a guy doing a BGP hijack and a route leak. This made it so some people could not use Cloudflare’s DNS resolver. A network in Brazil called AS267613 did something. They sent out a message saying they had the path to Cloudflare 1.1.1.1. This message was very specific. Because of the way the internet works this bad message was chosen over the one from Cloudflare. This meant that a lot of traffic was sent to the place. Over 300 networks were affected by this problem with Cloudflare 1.1.1.1.
MyEtherWallet was attacked by hackers in April 2018
They took control of a part of the internet address space owned by Amazon. This part was used for DNS servers. Had the address 205.251.192.0/24. The hackers then tricked the internet into thinking they were the MyEtherWallet site. They did this by announcing a specific route to the site. As a result people who tried to go to MyEtherWallet were sent to a site instead. This fake site was set up by the hackers to steal information. They wanted to get their hands on people’s cryptocurrency.
Many people lost their cryptocurrency because of this attack. The hackers stole from the victims. Amazon was involved in this incident. The attack happened in April 2018. MyEtherWallet users were affected badly.
Detection and Mitigation Strategies
To stop BGP hijacking we need to do a lot of things at the time. We have to be ready for it before it happens, watch for it all the time and act fast when it does happen. This means we need to have layers of protection, for BGP hijacking. We have to be proactive and keep watching what is going on with BGP hijacking. We have to be able to respond quickly to BGP hijacking when we see it.
Detection
BGP Monitoring and Anomaly Detection
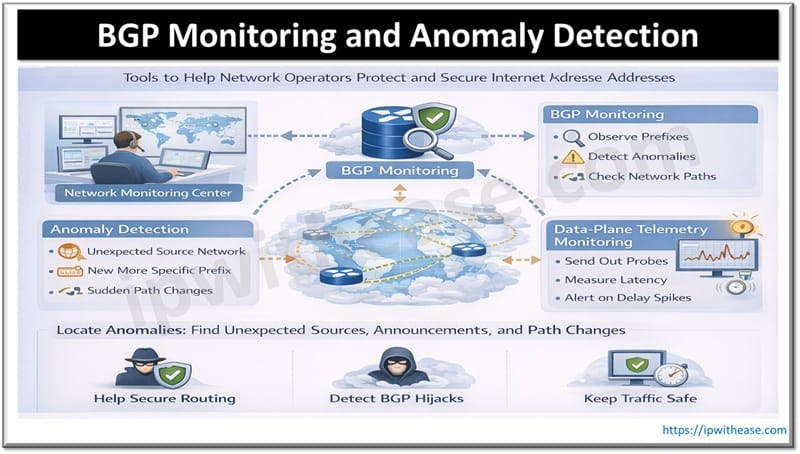
Network operators use services to check how their internet addresses are being routed around the world. These tools look for things like an unexpected source network, a new more specific internet address announcement, strange changes in the network path. These unusual things can be signs of someone taking control of internet traffic.
BGP monitoring helps to find these problems by keeping an eye on how internet addresses are being routed. It checks for anomalies in the network path. The goal is to catch changes that could be a sign of trouble. Network operators use BGP monitoring to protect their internet addresses. They want to make sure their traffic is being routed correctly.
BGP monitoring and anomaly detection are tools for this. They help to keep the internet running smoothly. BGP monitoring and anomaly detection tools are used to observe prefixes. These tools are essential for network operators. They use them to check their prefixes. The tools help to detect anomalies. Anomaly detection is a part of BGP monitoring. It helps to find changes. BGP monitoring and anomaly detection are used together. They help to keep the network safe. Network operators rely on these tools. They use BGP monitoring and anomaly detection every day.
Data-Plane Telemetry
Data-Plane Telemetry is really important. It helps operators check their networks by sending out probes and measuring things like how it takes for data to travel. This way they can find out if something is wrong. For example, Data-Plane Telemetry can detect if there is a delay in how long it takes for data to get from one place to another on a specific path.
If the delay gets a lot bigger all of a sudden that can be a sign that Data-Plane Telemetry has found a problem. It might mean that data is being sent through a network that is not supposed to be used. This can be a problem because it can mean that someone is trying to intercept the data. Data-Plane Telemetry can help operators find out if this is happening.
Mitigation and Prevention
RPKI and Route Origin Validation (ROV)
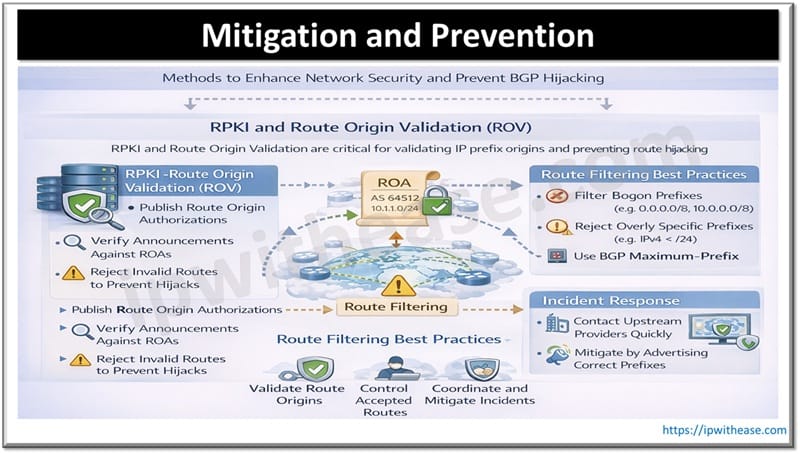
RPKI and Route Origin Validation are really important for keeping our networks safe. This is a step we can take to prevent problems. Network operators should make sure they publish Route Origin Authorizations. These are like messages that say which Autonomous System is allowed to announce specific IP prefixes. They are locked with a code so we know they are real.
Then other networks can use Route Origin Validation to check the messages they get from networks. They can compare these messages to the Route Origin Authorizations. Reject any that are not valid. This helps keep our networks safe by making sure the right people are in control of the IP prefixes. Route Origin Validation is a way to double check things and make sure everything is okay.
Route Filtering Best Practices
Networks should have rules to control the routes they get from customers and other networks. This means they should not allow prefixes, like bogon prefixes. They should also not accept prefixes that’re too specific, for example they should not accept IPv4 prefixes that are more specific than a Route Filtering Best Practices rule of /24. Networks should also use BGP Maximum-Prefix limits to stop things from getting out of control. This is like a safety switch, for Route Filtering Best Practices.
Incident Response
When something bad happens to a network like it is being hijacked the people in charge of the network can do things to try and fix it. The quickest thing to do is to get in touch with the internet service providers that are helping the traffic move and ask them to stop it. Another thing that can be done is to send out a message that says the good traffic is the one that should be followed which can help get the network back to normal because the internet uses a rule that says the most specific message is the one that should be used.
If things are really bad the people in charge of the network might have to change the addresses of the network, which’s, like updating a phone book and this is usually only done when there is no other choice during an Incident Response.
The best way to stop BGP hijacking is for everyone to use technologies like RPKI. This makes the internet routing system stronger. Route filtering also helps to prevent BGP hijacking. When more people use these technologies and apply route filtering the global routing table becomes more secure for all users. RPKI and route filtering make it harder for attackers to hijack BGP. As a result the internet is safer for everyone.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj