Table of Contents
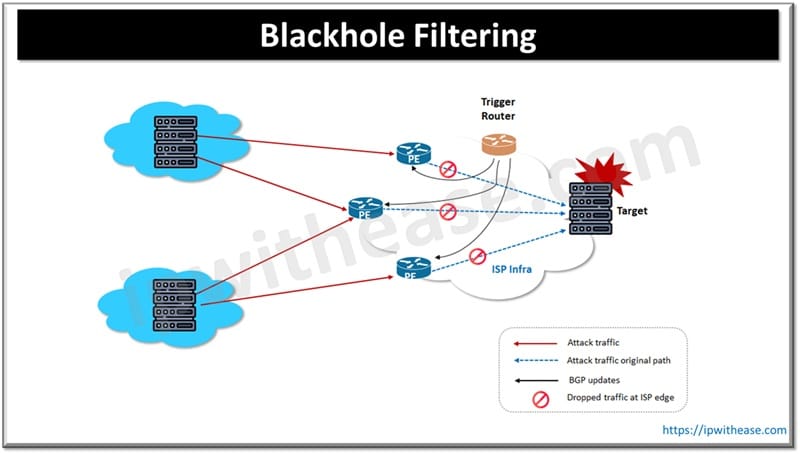
BGP backholing uses border gateway protocol (BGP) for traffic redirection to a null route meant for victim autonomous system (AS) and discards it. To implement BGP blackholing, BGP peering is required so network administrators can control traffic flow to their networks.
Border gateway protocol or BGP is a public network or Internet postal service and like any other routing protocols its aim is to ensure packet delivery to its destination with the shortest available path. BGP is defined in RFC 1654 as an exterior gateway protocol (EGP) and uses a path vector routing technique to achieve routing efficiencies.
Since public networks like the Internet are thwarted with threats, networks require a swift response at times to black hole attack traffic. In this technique Malicious and suspicious traffic is dropped before reaching the protected network.
In this article we will understand about BGP Back holing functionality, its purpose, what are the different techniques of black holing and its pros and cons.
Understanding BGP Backholing
BGP backholing is an effective technique to address DDoS attacks on the networks. DDoS attacks target a certain IP address or host and cause congestion on links which is used to connect adjacent networks. For the purpose of standardization on mechanisms of black holing, BGP community (RFC 1997) defines guidelines for operational ease. This allows network operators to drop malicious packets destined for specific IP addresses. Figure 1 below is presenting a typical black holing scenario where malicious traffic is dropped at the ISP edge.
Techniques of Blackholing
Let’s understand blackholing techniques:
- Route Advertisement – The route is advertised by network operators with black hole tag which indicates traffic to specific IP prefixes to be dropped.
- Traffic Filtering – Routers receive route update to recognize black hole tag and accordingly modify their routing tables to drop packets which match the advertised IP and discard it from being forwarded in the network
- Remote Triggered Black Hole (RTBH) – It lets initiate black holing remotely by network operators by sending signals to upstream providers on dropping unwanted traffic to prevent it from entering the network.
- Blacklists for Spam Filtering – It is another technique of black holing. Blacklists contain a list of IP addresses and their sources known for SPAM or other kinds of malicious traffic.
Applications of BGP Blackholing
- DDoS Attack Mitigation – BGP black holing effectively mitigates DDoS attacks and widely used by quick redirection of attack traffic to black hole
- Protection of Critical Infrastructure – In data centers and cloud services black holing stops malicious traffic before it reaches sensitive systems and causes damage or service disruptions.
- Automated Security Responses – BGP black holing can be integrated with automated security response system to allow rapid detection and containment of threats
BGP Blackholing – Routing Approach
Below are two commonly used approaches for implementing blackhole routing – Permanent static route approach and Trigger route approach.
Trigger Route
DDoS or malicious traffic detection is configured on a router which sends messages to other routers in the network to redirect traffic to ‘null’ route. This technique is effective in dropping or discarding malicious traffic in specific scenarios such as sudden intermittent spikes in traffic.
Permanent Static Route
Permanent static route configuration is implemented to redirect traffic from a specific IP address. When a specific IP address or host is the target of malicious traffic this technique is an effective way to redirect traffic to permanently ‘Null route’.
Black holing helps in mitigating DDoS attacks effectively but black hole routing can make an application / web server unavailable for legit users.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj