Active Directory Domain Controller
If you are able to visualize the process then it would not be difficult to find the differences between Active Directory and a Domain Controller.
The easiest way to remember the difference between both is that Active Directory handles your identity and security access and Domain Controllers authenticate your authority.
In other words, it can be said as the Active Directory Domain Service runs the domain controller.
Active directory:
Active Directory comprises of various services that work on the windows server and manage the access and permissions to the resourced network. It is the product developed by Microsoft.
It stores the data in the form of objects. These objects are single elements such as group, user, device or application. The categorization of the objects is done by the attributes and name which includes the information related with the user, for example, secure shell keys and passwords.
Related – What is a Forest in Active Directory?
Domain services are the main service of the active directory that comprises information of directory and communicated between the users and domain.
When the user signs in to the device or tries to connect with the server, this service validates the access. Domain services are the ones which have access to each resource.
There are several other services included in the active directory such as Certified Services, Lightweight Directory Services, Rights Management Services and Federation Services. All these services help in enlarging the capabilities of product’s directory management.
Related – What is a Tree in Active Directory?
The directory uses the tiered layout that comprises of domains, trees and forest. It is the major features of active directory domain services and helps to coordinate between the networks.
Domain Controller:
A server that gives the response to the verification requests and confirms the users on the computer networks are known as a domain controller. It helps to organize the computers and users that work simultaneously on a similar network in a hierarchical way. The controller helps to retain all the data in an organized manner and also keep secure.
The domain controller (DC) is considered as the key for the active directory (AD). Attackers are aware of all the tricks used to fetch the data including the DC itself. Though you are not able to protect your DCs from the attackers these DCs can help to find out the cyber attacks.
The primary function of the DC is to validate and authenticate the user that has access on the network. They are responsible for checking the username, passwords and other credentials, as well as they, have the right to allow or deny the user who is trying to access.
The most common example is the Microsoft Azure AD or Microsoft Active Directory, whereas there is a Linux based directory named as samba which is equivalent to a domain controller.
The importance of the domain controllers is that they comprise of the data which determines and verifies the access to your network and also includes the group policies as well as computer names.
During the cyberattack, the domain controller is the primary target as it includes all the data and network that an attacker can cause massive damage.
Active Directory vs Domain Controller (ad vs dc):
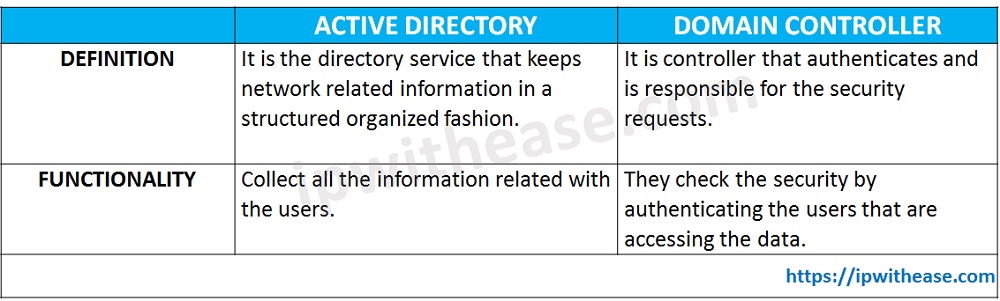
Definition
A directory service produced by the Microsoft for the networks of windows domain is known as the active directory whereas a server that responds to the authentication security requests such as checking permissions, logging in, etc. for the window domain is known as a domain controller.
Function
The main function of the active directory is to store information regarding all the resources and users in an organized and well-planned manner.
In contrast with it, the domain controller is assigned with the task to perform the authorization and authentication of the users for accessing the resources.
Below table summarizes the domain controller active directory difference:
| ACTIVE DIRECTORY | DOMAIN CONTROLLER | |
|---|---|---|
| DEFINITION | It is the directory service that keeps network related information in a structured organized fashion. | It is controller that authenticates and is responsible for the security requests. |
| FUNCTIONALITY | Collect all the information related with the users. | They check the security by authenticating the users that are accessing the data. |
![]()
Download the difference table here.
Related – Active Directory Interview Questions
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj