Active Directory Forest –
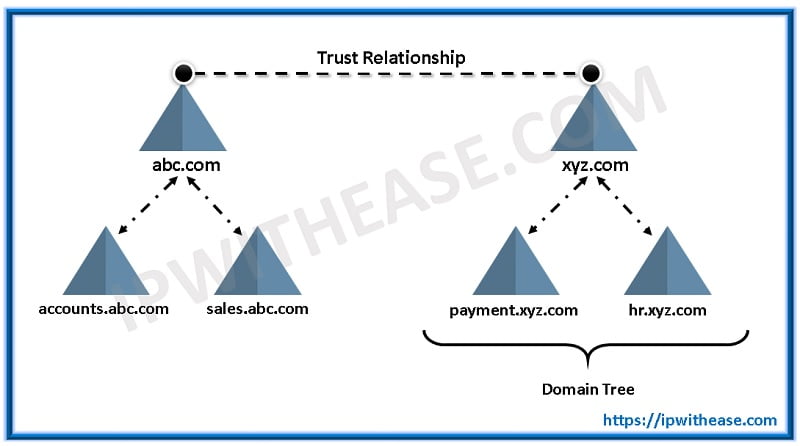
A Active Directory Forest is the collection of more than one domain trees having different name spaces or roots. This means that the forest contains a number of domain trees that do not share a common name space, or more so, do not have the same parent domain.
But, for all the trees in the forest, there is one common configuration and global catalogue.
The trees in the forest are also under transitive trust relationship with each other. A forest does not require a specific name.
A forest’s trees form a ranking or hierarchy for trust. At the root of the trust, tree is the tree name which refers to the forest.
How is a forest unique from each other? It is the configuration of the forests. Each forest shares a common configuration.
What is the configuration? It is the way in which the domains are stored in the Active Directory.
Related Active Directory Interview Questions
The configuration is the database of the forest, but, each domain of the forest possesses its own copy of the database according to the configuration.
The trees in the forest trust each other, meaning the user of any specific domain of that forest can have access to all other resources in that same forest in which they are working.
As explained above, there is a separate database for every domain in the forest. So, for the users to access or search for a resource in a domain, Domain Controllers are made the Global Catalogue Servers.
Related – LDAP vs Active Directory
These Catalogue Servers have information of every domain/object in the forest. Searches can be conducted based on this information.
Structure in AD Forest:-
There can be 3 kinds of structures or models of forest in an active directory:-
- Resource forest structure
- Organizational forest structure
- Restricted access forest structure
Combinations of these structures are required to cater to the needs of different users in an organization.
Resource Forest Structure:-
A completely separate forest is made to manage the resources. Only accounts of server administrators, alternate user accounts to provide access, in case of user accounts vanishing from the organizational forest.
Trust is built so that other users of other forests are able to access the resources of that resource forest. It protects those network areas that need to keep operating even in states of other network areas breaking down.
Organizational Forest Structure:-
The user accounts and resources are contained in this structure and are independent. This forest can be used to provide service or data isolation or service autonomy if it is configured to be inaccessible by users outside the forest.
To access resources of other forests, trust needs to be built up between the organizational forest and other willing-to-be-accessed forest. Every AD has at least one organizational forest structure.
Restricted Access Forest Structure:-
An individually separate forest is established in which data and user account that are to be kept independent of other organizations in the restricted access forest structure.
When it is extremely possible to lose/compromise the data of the project, this forest structure provides data isolation.
Other forest users cannot access this forest as it does not trust any other forest. Users’ accounts are present in the organizational forests for accessing general resources.
Related – What is Tree in Active Directory?
For accessing restricted resources, a separate user account is required in this restricted access forest structure.
So for this, the user needs to have two different workstations, one connected with organizational forest and other to restricted access forest.
Characteristics:-
- Single Configuration: It defines what attributes the data (domains) are sorted. The domain controller in the forest has that same configuration.
- Common Global Catalogue: Some attributes from each data/object is replicated to the global catalogue. The catalogue helps to search and login to the directory. This allows us to efficiently using the information on the directory.
- Common container of Configuration: This container stores data of Active Directory for the forest. Information contained is sites, services, directory partitions and directory-enabled applications. Container’s name format is cn=configuration, dc=forestRootDomain. Any kind of edits to the container is copied to all domain controllers inside the forest. Enterprise Administrators have complete control of the container.
- Transitive trust: Two-way trust is automatically built between the domains of the forest. Consequently, groups and users of any domain can be entered in the list of access control.
Related – Domain Controller vs Active Directory
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj