Table of Contents
What is DNS Proxy?
DNS proxy is used to manage DNS queries and forward requested queries to specific name server. It forwards DNS query and response to DNS server and DNS client respectively. DNS Proxy stores client queries in the device which speed up the traffic connection for repeated queries. In short it maintains a cache in the device database and uses it for recurring connections.
DNS Proxy Cache
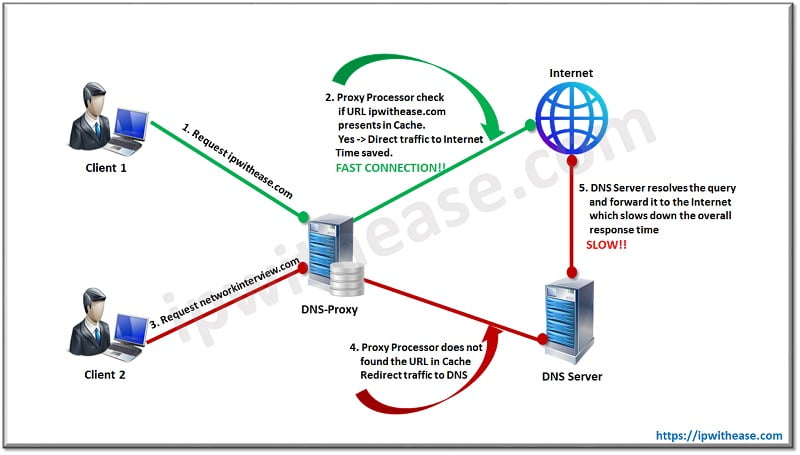
Let’s discuss DNS Proxy Cache. Caching option allows DNS proxy to unburden remote DNS servers and speed-up response time for DNS lookups.
When someone initiates connection to a DNS server, a DNS query is resolved by a DNS proxy and the corresponding request is saved in the device’s DNS cache. This stored cache helps the device to resolve following queries from the same domain/webpage and avoid network latency delay.
Sometimes proxy cache is not configured in the device, in that scenario client machine query directly hits connection to configured DNS server which increase delay in response time and degrade connection performance
Figure 1.1 illustrate the whole process step-by-step
Why is DNS Proxy used?
Obviously, we should use DNS-Proxy to avoid network latency. It’s a universal fact that most of the DNS-Proxy is deployed to get faster response. However, another factor which DNS-Proxy plays is to secure your network from malicious attack. How…?
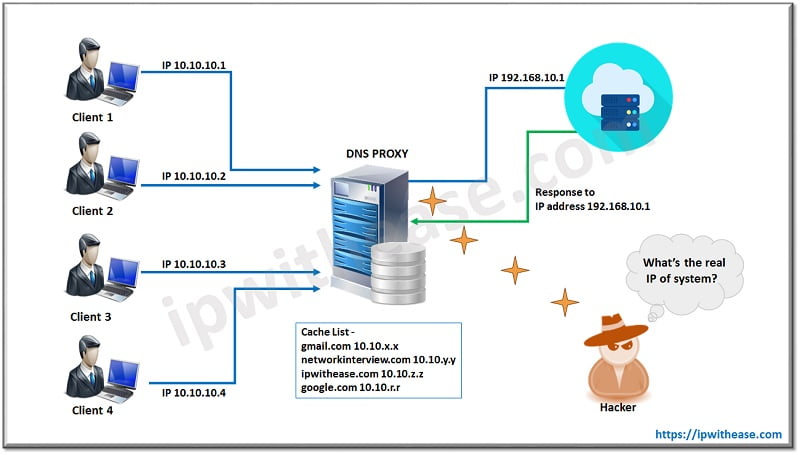
Let’s understand through a diagram. Fig 1.2
- Source clients are having 10.10.10.x range through which connection towards the internet is initiated.
- DNS-Proxy server plays an intermediate device which receives clients request and forward it to Internet
- Clients IP address performs NAT (Network Address Translation) ** NAT is used to translate local IP address to Public IP address** with DNS-Proxy Public IP. For example, the real IP address is 10.10.10.1 which translates to another IP address 192.168.1.10 (NAT IP). It can be One-to-One OR One-to-Many.
- In such a way, attacker not able to get downstream network detail when trying to fetch internal IP address from DNS-Proxy connections
- This process secures the network from any intruder attack.
DNS Proxy Scenarios
DNS Proxy with Split DNS
We can split DNS query based on interface and hostname. We can deploy a name server in the network and assign domain names with them. When a user query initiates a query to the assigned domain name, the server redirects request to associated name servers. Each DNS proxy must be associated with the interface, which means if the DNS proxy feature is not configured on the firewall, all traffic forward to firewall/switch/router (all L3 network devices) will be dropped.
Figure 1.3 shows how DNS proxy is placed in the split domain topology based on Name Server
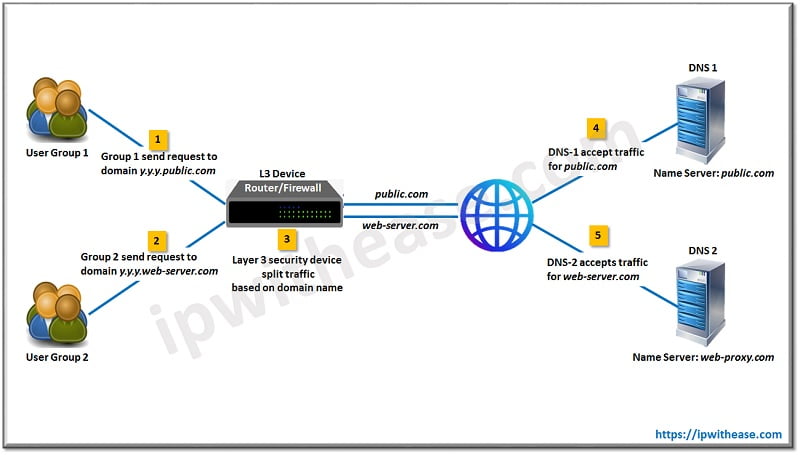
- User Group-1 and User Group-2 make two queries—y.y.y.public.com and y.y.y.wbe-server.com which points to L3 device (either router or Firewall) implemented as DNS server with DNS proxy enabled. [y.y.y can be any name associated with domain]
- Further, DNS proxy feature redirects the y.y.y.public.com, the query to .public.com Name server
- While the y.y.y.web-server.com query is redirected to .web-server.com Name server.
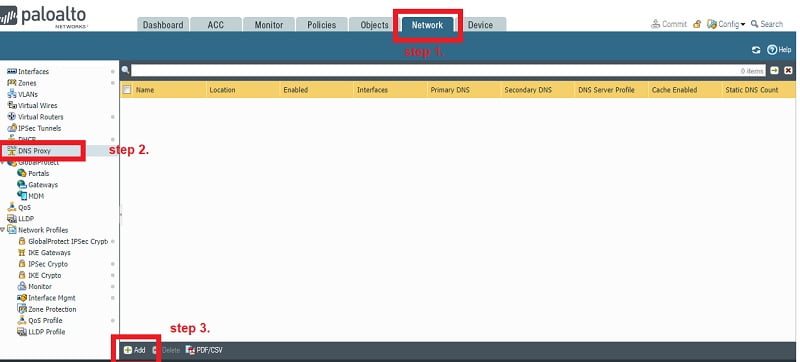
How to configure DNS Proxy in Palo Alto Firewall
Pre-requisites
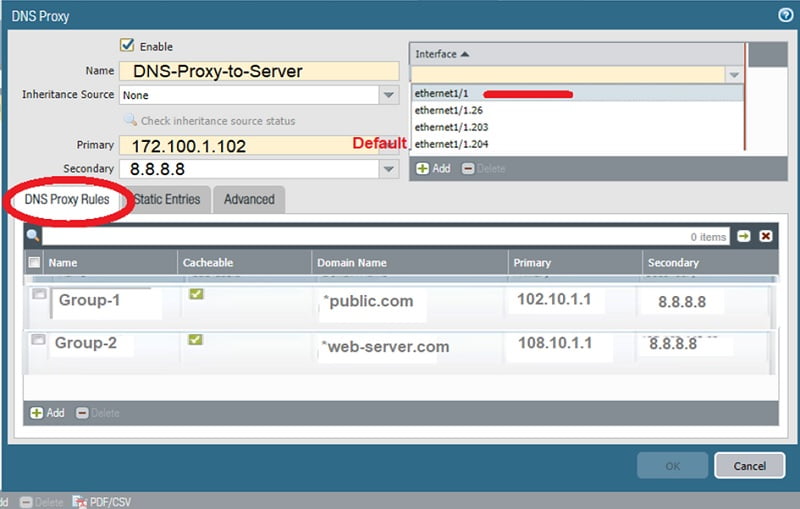
- Bind DNS Proxy with an Interface, here we take ethernet1/1
- Default DNS should be configured in the firewall, 172.100.1.102
- DNS name server, where customized traffic will be forwarded as per mentioned domain name
- Security policy to allow traffic for DNS server over port TCP-53 and UDP-53
Configuration steps
Static Entries
Allows you to configure static FQDN-to-IP address mappings that store in Palo alto firewall cache and revert to host without sending connection request to DNS. Example we can add the URL ipwithease.com whose IP address is 156.10.1.122. Response comes back from the firewall without forwarding the query to the DNS server. It reduces response time and makes connections faster.
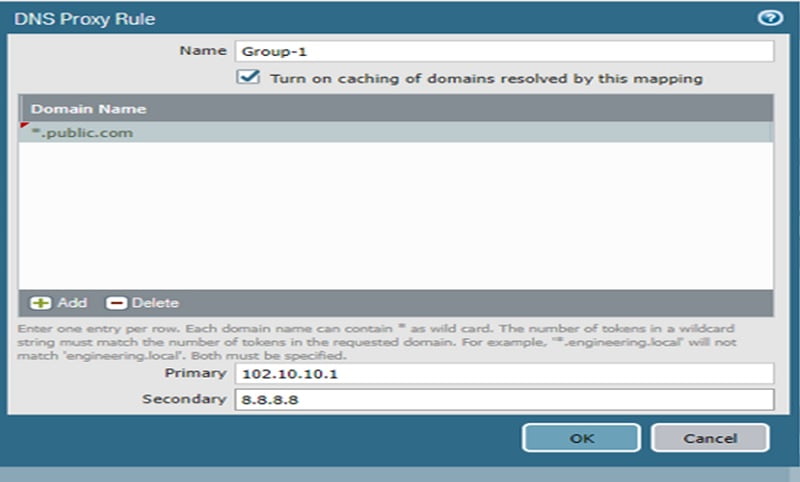
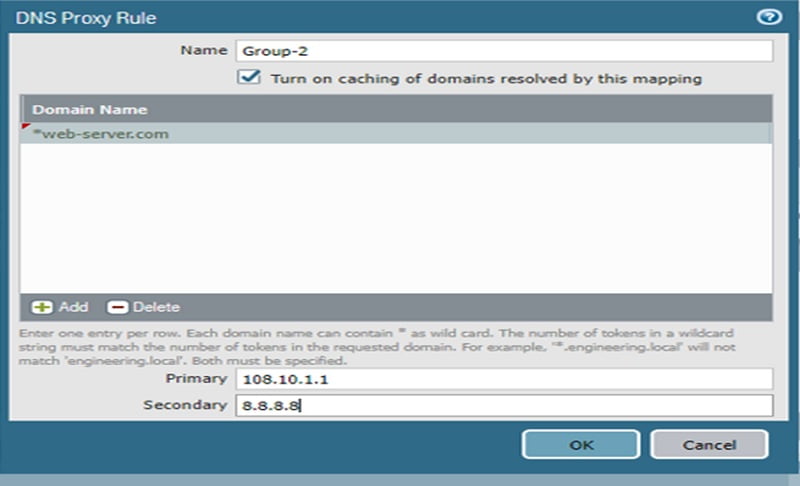
DNS Proxy Rules
Allows you to add customized domain names and matching primary and secondary DNS servers to resolve queries that match the rule. The firewall searches for a match in the DNS proxy if the domain name is not available in the DNS proxy cache and redirects the query to a respective DNS server based on the match policy. If no match is found in DNS proxy rules, the firewall sends the query to the default DNS primary and secondary servers. Example: – when traffic comes for public.com it will redirect to DNS server 108.10.1.1. Moreover, if in case 108.10.1.1 is not responding, it will forward to global DNS 8.8.8.8
Example
- The DNS request of Group-1 is regularly proxy to DNS server 102.10.1.1 for domain name *public.com
- The DNS request of Group-2 is recurrently proxy to DNS server 108.10.1.1 for domain name *web-server.com
- If no match found for any domain in proxy rule, it is redirected to default DNS server which is 172.100.1.102
Go to Network🡪 DNS Proxy🡪 Add🡪DNS Proxy Rule (Group-1, Group-2)
Add inputs in DNS Proxy Rules and commit the changes.
Conclusion
DNS proxies are useful in a network where a split traffic model is required. Caching feature in DNS proxy helps to reduce query response time, avoid latency, and makes the network more secure which prevent attacks in the organization.
Continue Reading
How to Configure Cisco Router as DNS Server
How to configure DNS Sinkhole: Palo Alto Networks
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj