CONFIGURING PRIVILEGE LEVELS IN CISCO IOS
CONFIGURING PRIVILEGE LEVELS IN CISCO IOS
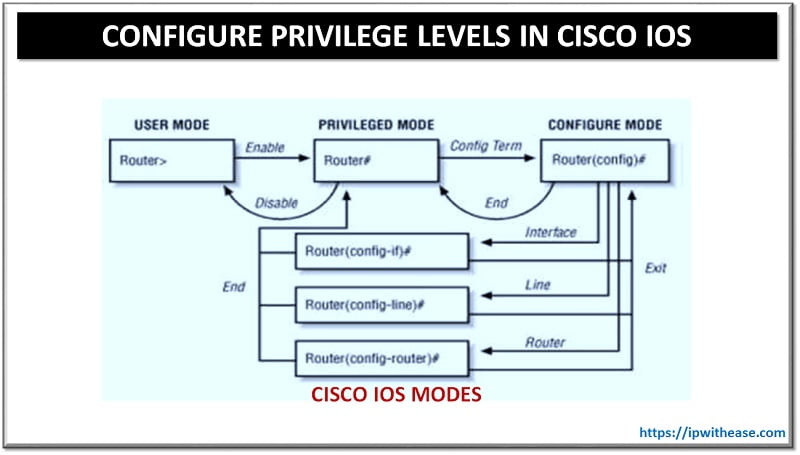
Privilege levels determine who should be allowed to connect to the device and what that person should be able to do with it. The Cisco IOS software CLI has two levels of access to commands –
- User EXEC mode (privilege level 1) – Provides the lowest EXEC mode user privileges and allows only user-level commands available at the router> prompt.
- Privileged EXEC mode (privilege level 15) – Includes all enable-level commands at the router# prompt.
Apart from these 2 modes, additional levels can be configured between 2 to 14 for protecting the network devices from unauthorized access. Customized Privilege levels are useful for enterprises which can’t invest in authentication servers.
Below is a configuration examples to create a customized Cisco Privilege Levels 10, which should include Privilege to –
- configure terminal
- configure interfaces with IPv4 addresses
- shut interface
Step 1 –
Configure “enable secret” password for Privilege Level 10
R1(config)#enable secret level 10 Cisco123
R1(config)#exit
Step 2 –
Configure Privilege Level 10 to move to Global Configuration mode, configure interfaces with IPv4 addresses and shut the interface.
R1(config)#privilege exec level 10 configure terminal
R1(config)#privilege configure level 10 interface
R1(config)#privilege configure level 10 ip address
R1(config)#privilege interface level 10 shutdown
R1(config)#privilege interface level 10 no shutdown
R1(config)#privilege interface level 10 no ip address
R1(config)#exit
Step 3 –
Now , we will verify Privilege Level 10 as below –
Password:
R1#config t
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)#int fa0/0
R1(config-if)#ip address 10.10.10.1 255.255.255.0
R1(config-if)#no shut
R1(config-if)#exit
R1(config)#exit
Step 4 –
Below verification validates that configured Privilege level 10 does not allow other parameters to be configured apart from ones required (like Privilege level 10 can’t be allowed to configure ipv6 address ) –
% Unrecognized command
Related – PIPE Feature & Commands in Cisco IOS
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj

 CONFIGURING PRIVILEGE LEVELS IN CISCO IOS
CONFIGURING PRIVILEGE LEVELS IN CISCO IOS