ISP and enterprise organizations deploy routers from several vendors to leverage standardized routing protocols of OSI layer such as BGP so as to enable interoperability between control planes of different routers. But standardized protocols are not getting evolved in a quick manner, it takes enormous time to document, standardize, implement and then deploy new BGP features. And at times many features requested to be included in standardization are often not considered to be included as part of documentation.
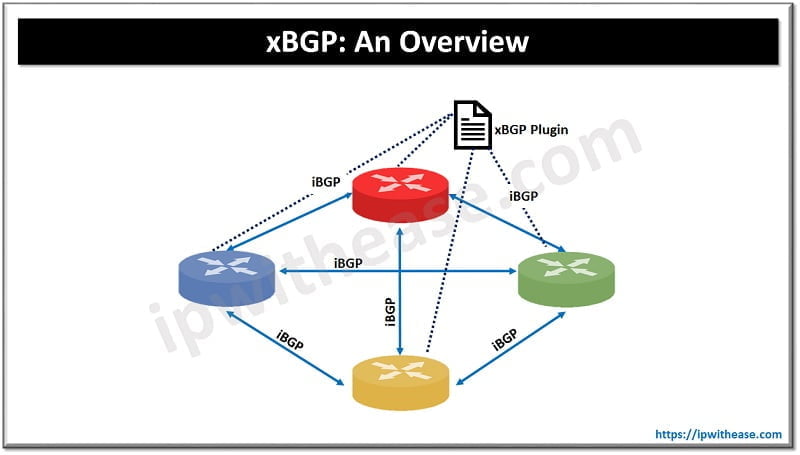
xBGP proposes a mega shift which enables network operators to customize routing protocols deployed in their networks as per their requirements.
Today we look more in detail about xBGP framework which lets network vendors to use underlying BGP protocol and over that additional feature are deployed, how it works, its advantages etc.
What is xBGP?
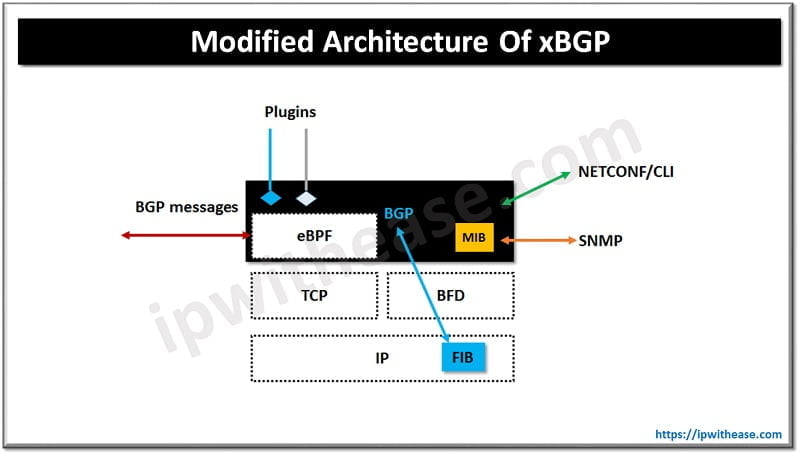
xBGP is a framework which makes any BGP implementation more flexible. It is a vendor neutral API which exposes the key data structures and functions of any BGP installations or deployments. Each xBGP compliant installation includes an eBPF virtual machine which executes the operator supplied programs. FRR routing and BIRD is extended to support xBGP. Network operators can write their own BGP extensions and run it on BGP compliant routers in their networks. Network programmability is achieved at control plane level using this.
Add new features to xBGP
The BGP basics are defined in RFC4271. Each BGP deployment must adhere to this standard to be able to establish a session with another router running BGP installation. A simple BGP workflow is depicted here.
- Router receives a BGP message
- If the message is BGP UPDATE it will be first checked for the importation side of the router. If the route passes import policies, then it is installed in a specified data structure named Adj-RIB-in
- Accepted route is copied to Loc-RIB data structure which contains all accepted routes from neighbouring speakers
- The BGP decision is executed for every route updated in Loc-RIB and one BGP route is selected towards each prefix known to router
- The accepted routes are inserted into Adj-RIB-in
Insertion Points Defined by xBGP
The xBGP uses BGP workflow to place insertion points. Insertion points are BGP implementation locations where the operator provided bytecode can be executed. Five insertion points are defined by xBGP:
- BGP message from peers – Plugin insert at this point will decode messages received from neighbours. eBPF bytecode insertion here will decode the new BGP attributes (CLUSTER_LIST and ORIGINATOR_ID)
- Importation filters is dedicated to import filter to check if its router-id (or cluster-id) is contained in either CLUSTER_LIST or ORIGINATOR_ID
- BGP decision process can add new steps to the BGP decision process or change existing . router reflectors implementation requires to change this
- Exportation filters – export filters handling is taken care and route is exported according to section 6 of RFC4456
- BGP message to peers is serialization of BGP messages which will be transported over wire. The cluster list and originator ID is must to add here
How to write Plugin for xBGP
Network operators can write their own BGP extensions using C language. The API plays a key role in creation of new extensions. As the plugin execution is independent of host BGP implementation it will not directly access the data structures maintained with the host. xBGP supports host implementation hence, API allows conversion of internal structures to a neutral representation which can be manipulated by plugin.
Continue Reading:
Difference between iBGP & eBGP
Are you Preparing for your Next Job Interview?
If you want to learn more about BGP, then check our e-book on BGP Interview Questions and Answers in easy to understand PDF Format explained with relevant Diagrams (where required) for better ease of understanding.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj