Introduction to F5 BIG-IP
“F5 BIG-IP ” has ability to function as full proxy. Full Proxy design of F5 BIG-IP is a wonderful tool through which one can manipulate client-side connections and server-side connections all the way through the application layer. All this is possible because of F5’s powerful feature set of BIG-IP “iRule”.
Functions of iRule in F5 BIG-IP
iRule can perform buffet of functions like –
- making load balancing decisions
- modifying packet content
- directing traffic flow
- collecting statistics
and plethora of others things up to layer seven. iRule gives great deal of power and control over your network, Traffic, Routing and application flow programmable. iRules are available in LTM/GTM/ASM Modules. iRules are created with the help of Tool command language (TCL) programs or script (Also called as Event handler) that are assigned to Virtual server and run by one or more user specified Events related to the Virtual server, such as HTTP get request or new TCP connections.
Example Scenarios
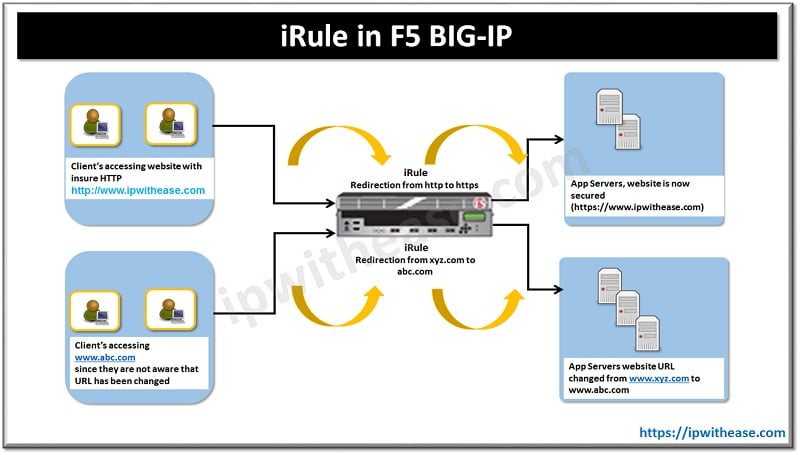
Some of common scenarios where iRule plays a pivotal role are –
Case 1 –
User sends an insecure http request to website (let’s say in this case it is www.ipwithease.com) but actual page which is opening is https.
Case 2 –
Sometimes whole URL gets changed, like in case a user tried opening www.abc.com , however resultant request is redirected to www.xyz.com.
The power of iRule makes both the above shared cases possible. As in case 1, the benefit is that we don’t need to broadcast every client that we have changed our security and have moved from insure (HTTP) to secure (HTTPS).
Structure: iRule in F5 BIG-IP
Lets further understand the iRule structure in more detail.
iRule Structures are composed of –
- Event Declarations and
- TCL Execution Code
When a certain event occurs, match the condition and then perform the action
Below is the format –
If { condition_expression } { Action_when_condition_true } else { Action_when_condition_false } }
Let’s use CASE 1 example where where http to https redirection is required –
switch [string tolower [HTTP::host]] { “ipwithease” { HTTP::redirect “https://ipwithease.com” } } }
Continue Reading:
BIG IP F5 High Availability Guide
TMOS components of BIG-IP (Traffic Management Operating System)
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj