Table of Contents
Proxy Auto-Configuration (PAC)
PAC file or Proxy Auto-Configuration (PAC) is coded in JavaScript language and contains set of rules. Web-browser takes decision to traffic based on set of rules defined in the PAC file. Basically, it is a programming script which instruct browser to redirect traffic as per the instruction in the code. PAC file is the advanced feature which is used in Proxy server now-a-days. PAC file tells proxy server how to direct traffic for specific destination.
In JavaScript language, function code FindProxyForURL (url, host) is defined to redirect the traffic as per the organisation requirement
- Direct – Traffic directly goes to the internet if Direct is mentioned in the code
- Proxy—Traffic will redirect to the IP address which is specified in the Proxy. We can specify multiple proxy server IP addresses.
How does the PAC file work?
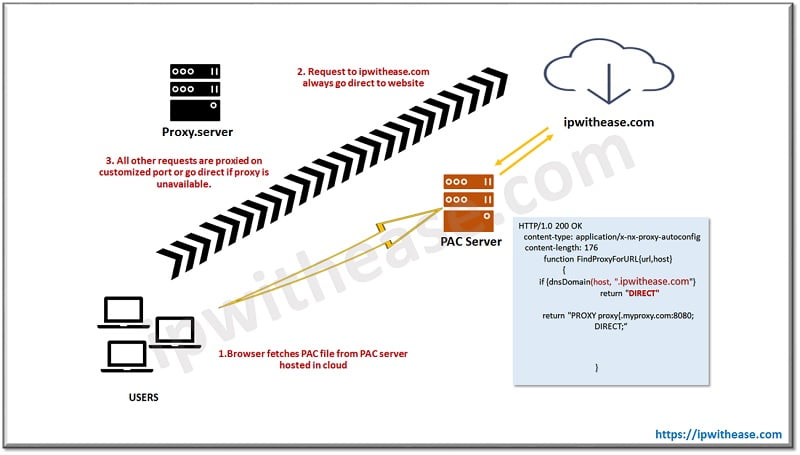
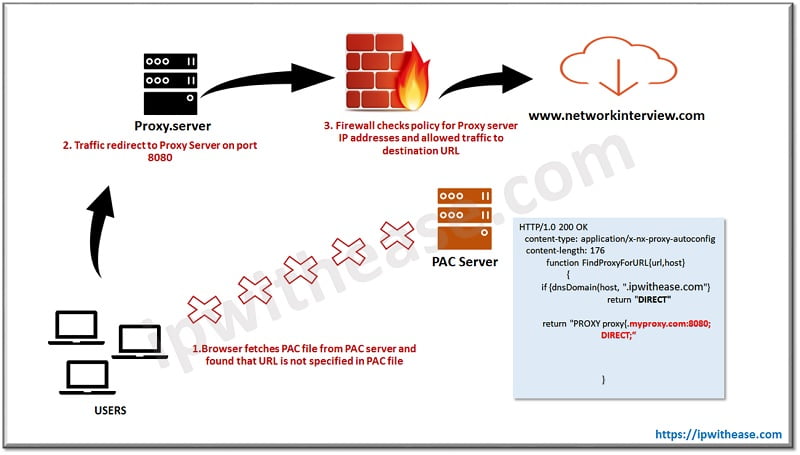
Here is an overview of how does the PAC file work and how it passes traffic based on domain name.
- First step is to fetch PAC file by Browser which is directed by Browser setting.
- The URL for the PAC file defined manually in the PAC script, forward to the Browser using any internal AD Group Policy Object (GPO) or discovered using an auto-discovery protocol. The file itself may be hosted on an internally managed server, or on the cloud. We recommend that you should host your PAC files on internal location because of security reason.
- Browser parse the JavaScript file (PAC file) and understands the statement which is defined in the script. It sees that if URL contains domain ipwithease.com, then it should access the site directly.
- For any other site it should go through Proxy server over customised port (80,443,8080 etc.)
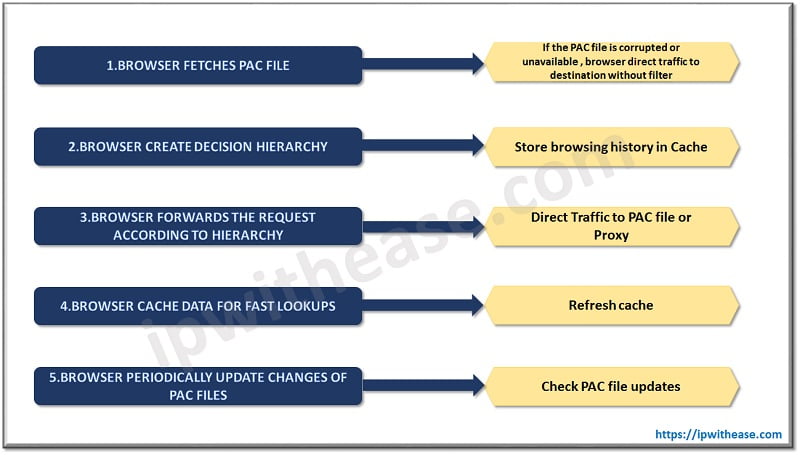
How does browser process PAC file?
- Browser should be configured in such a way that it can retrieve PAC file script for URLs and forwards traffic according to the instruction defined in the programme.
- If in case browser unable to open PAC file or unable to retrieve data from PAC script , browser forwards traffic Direct to destination without any filter.
- Once PAC file is retrieved, the Browser will parse and create a cache which is stored as a history in browser backend script. This allows the Browser to make ultra-fast-forwarding decisions, without taking reference to PAC file.
- The Browser will check intermittently for PAC file updates, we can customize the PAC file update. Admin can set timer periodically to sync PAC file latest update with browser.
Recommendations: Where to host PAC files
- Must be hosted in secure place
- Integrity must be maintained (no one can access and change the script)
- SSL/TLS algorithms must be used to secure the PAC file connection
- Easy for users to connect with PAC file without any latency/delay
- Should recommend to host .pac file internally instead of placing it on outside cloud.
PAC file default syntax
- Mostly and primarily used function in PAC file code is FindProxyForURL(url, host) : which has two statements: 1. url is the URL of the requested destination; and 2. host is the host name who has requested the url.
- isPlainHostName which returns true if the destination hostname contains no dots, example, http://ipwithease. Technically it is used for the sites which are hosted locally in the network.
- dnsDomainIs check hostname and returns true if match found in the script. Example
if (dnsDomainIs(host, ".network.com")) return "DIRECT";- localHostOrDomainIs check hostname and only redirect the traffic through PAC file script if exact match found.
if (localHostOrDomainIs(host, "www.ipwithease.com")) return "DIRECT";- isInNet which returns true if the IP address for the destination host name resolves to the specified subnet.
if (isInNet(host, "10.10.0.0", "255.255.0.0")) return "DIRECT";- dnsResolve resolves the destination hostname (or a static FQDN) to an IP address, it reduces dns lookup for same domain.
var resolved_ip = dnsResolve(host);
if (isInNet(resolved_ip, "10.0.0.0", "255.0.0.0") ||
isInNet(resolved_ip, "192.168.0.0", "255.255.0.0") ||
isInNet(resolved_ip, "10.10.10.0", "255.255.255.0"))
return "DIRECT";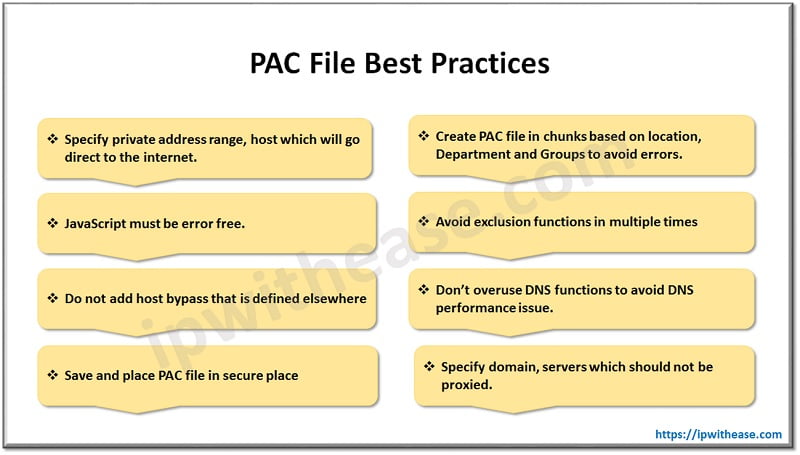
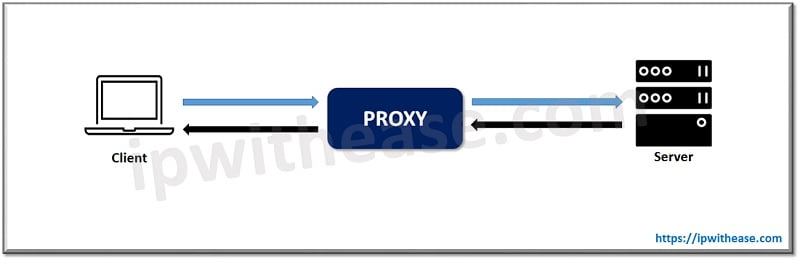
Proxy Server
A proxy server is a device/software that provides a gateway between intranet and internet. It can be hardware or software device which is capable to filter traffic at the application layer (Layer 7).
PAC file redirect traffic to the URLs(destination address) which are defined in the script. However if the URL doesn’t exist in code then traffic is going via Proxy server. Proxy server performs 2 way communication, first communication happens between client to Proxy server and second connection established between Proxy server to destination server.
Proxy sever Connection-flow
Lets take an overview about proxy sever connection-flow
- User requests access to internet for URL networkinterview.com through protocol HTTP
- System’s browser checks if the URL exists in the PAC file
- URL is not configured in the PAC file hence traffic redirected to Proxy server on port 8080
- User system is trying to attempt connection to Proxy server and send SYN packet to server
- Proxy server accept the traffic and forward it to next-hop firewall.
- Firewall checks rule in the policy and if policy is allowed for proxy server, traffic redirect to destination
- Requests made through the user-to-proxy connection then the proxy-to-Firewall(destination) connection will be analyzed to ensure they are correct and fulfil with the defined policy until either side terminates the connection.
Difference: Proxy and PAC File
Proxy and PAC files, both technology forwards source traffic to destination URL on port 80, 443 and FTP. However, their deployment depends on infrastructure of any organization. PAC file is highly recommended for small scale companies whereas Proxy hardware should be used where large number of users exist.
Proxy servers are address and port based, with higher level of configuration like policy, SSL, exception list, SAML, browser customization, URL filtering. On the contrary, PAC files are programming language with simple JavaScript codes. Monitoring and filtering of traffic is available in Proxy server whereas PAC file only store cache and take decision on behalf of hierarchy tree.
Comparison Table
Let’s summarize the differences between the two:
Features | PAC File | Proxy |
|---|---|---|
| Device Type | PAC file run in browser sandbox hence it has limited features. | Proxy Server can be hardware or software ; it has multiple features based on downstream traffic. |
| Hostname Features | It cannot identify hostname of user’s machine. | It can identify hostname or UID of systems. |
| Traffic Parsing | It is simple scripting language which parse URLs based on domains , locations and groups. | It can parse traffic based on SSL , policy , port. |
| Failover | Support proxy failover, bypass. | Need addition infrastructure to deploy proxy in cluster to implement failover feature. |
| Language | Requires JavaScript Language. | No language is required to run commands, GUI is available . |
| Authentication | External authentication servers are required. | We can specify AD servers in device settings to forward traffic for authentication. |
| Scope | Limited to small number of users , easy to deploy though. | Can implement in large setup, require expertise in deployment. |
Conclusion
Both Proxy and PAC files provide security to network infrastructure. The more you explore, the more you achieve. As per security point of view, both technology helps to prevent attacker from invading any network from outside world. Blacklisting feature in proxy helps admin to block malicious URLs which supports to make network more secure and safe for downstream users.
In short, proxy and PAC file can keep the internal network secret and secure from intruders.
Continue Reading
PROXY vs NAT – Understand the Difference
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj