SSL VPN technology has earned popularity in recent years. Like its IPsec counterpart, SSL users to connect remotely back to their home organization, obtaining access to restricted network resources. There are several different variants of SSL VPN architecture and an increasing number of vendors and Open Source projects providing solutions.
IPsec VPN technology is used for both end user and site-to-site connectivity while SSL VPN technology is used exclusively for user connectivity and provides an ideal solution for creating a VPN tunnel through restricted networks back to the home site.
What is SSL VPN?
An SSL VPN (Secure Sockets Layer virtual private network) is a form of VPN technology that can be used with a standard Web browser. In contrast to the traditional Internet Protocol Security (IPsec) VPN, an SSL VPN does not require the installation of specialized client software on the end user’s computer. It’s used to give remote users access to –
- Web Hosted applications
- Client/server applications and
- Internal network connections.
A virtual private network (VPN) provides a secure communications mechanism for data and other information transmitted between two endpoints. An SSL VPN consists of one or more VPN devices to which the user connects by using his Web browser. The traffic between the Web browser and the SSL VPN gateway is encrypted via the SSL protocol or its successor TLS (Transport Layer Security) protocol.
Related: 4 Different Types of VPN
SSL considers following as its key Goals
- Confidentiality of Information
- Data Integrity
- Authentication of Server
- Authentication of Client
Below are benefits of SSL Virtual Private Networks:
1. No client software required for accessing web-enabled applications
Benefit: deployment, management and administration extremely simple and effective
2. SSL is a de-facto standard
Benefit: interoperability between different vendors and applications
3. Included as default in a number of web browsers
Benefit: no client software required
4. As commonly deployed, only servers require digital certificates to establish the encrypted session
Benefit: Reduction in the requirement to manage certificates
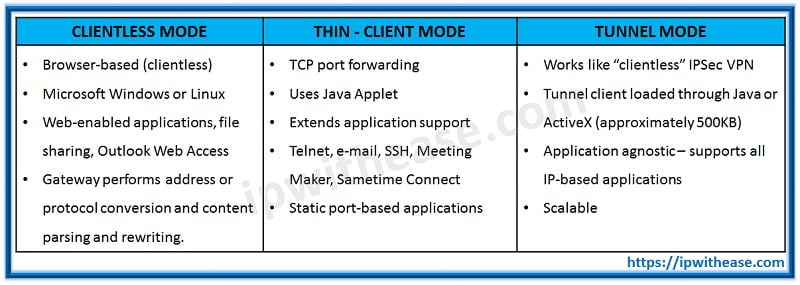
SSL VPN works in three modes explained as below:
Clientless—
Clientless mode provides secure access to private web resources and will provide access to web content. This mode is useful for accessing most content that you would expect to access in a web browser, such as Internet access, databases, and online tools that employ a web interface.
Thin Client (port-forwarding Java applet)—
Thin client mode extends the capability of the cryptographic functions of the web browser to enable remote access to TCP-based applications such as Post Office Protocol version 3 (POP3), Simple Mail Transfer Protocol (SMTP), Internet Message Access protocol (IMAP), Telnet, and Secure Shell (SSH).
Tunnel Mode—
Full tunnel client mode offers extensive application support through its dynamically downloaded Cisco AnyConnect VPN Client (next-generation SSL VPN Client) for SSL VPN. Full tunnel client mode delivers a lightweight, centrally configured and easy-to-support SSL VPN tunnelling client that provides network layer access to virtually any application.
Comparison: Clientless vs Thin-client vs Tunnel mode
SSL VPN Connection Stages:
Below diagram shows step wise exchange of information between Client and SSL VPN gateway before Full SSL VPN connection is established. A TCP connection on port 443 is made to the SSL VPN Gateway in the first instance to allow an SSL protocol handshake where the SSL certificate for the VPN Gateway is checked for validity. If the certificate has been revoked the connection will be torn down, otherwise minor errors are reported to the user and a correct certificate allows the exchange of user credentials before the tunnel is established. Many vendors also allow automated client updates at this stage. Once the below stages have been traversed, users can utilize SSL VPN connection to access corporate/office LAN securely.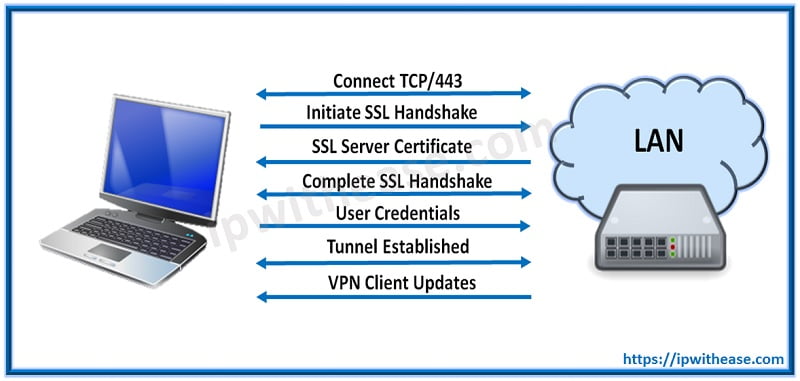
Continue Reading:
SSL vs TLS: What is the difference?
IPSEC vs SSL : Detailed Comparison
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj