Table of Contents
SSL (Secure Socket Layer) and TLS ( Transport Layer Security) are 2 commonly used protocols for data secured data transfer between a web server and a web browser (client machine). Both protocols render authentication and encryption when transferring data between client and server. TLS is a more recent, improved and secured version of SSL. Also, It fixes some key security vulnerabilities found in earlier SSL protocols. It is important for websites to Get SSL Certificate to secure communication between user and server and safeguarding the sensitive information.
How SSL/TLS work
When SSL/TLS certificates are provisioned on web server, 2 keys are used – (1) public key and (2) private key. The keys are used for encryption and decryption data between server and client.
Now, when a request is initiated by any visitor or client PC through browser, it will look for server site’s SSL/TLS certificate. Next, the browser will perform a secured “handshake” to validate certificate and authenticate the web server. Once the client PC browser validates the authenticity of certificate, an encrypted link between client browser and server is created for transport of data.
SSL/TLS History
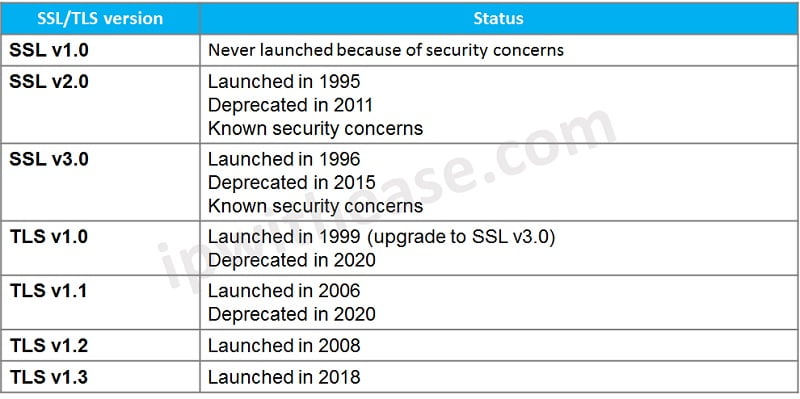
SSL was developed by Netscape. SSL had gone through some updates in its 3 version. Though its 1st version (SSL v1) was not considered an official launch, its 1st approved version was SSL v2, which was launched in year 1995. Below are the 3 releases of SSL –
- SSL v1
- SSL v2
- SSL v3
SSL3.0 was prone to man in the middle attack. One such case was “POODLE” vulnerability which allowed attackers to encrypt and decrypt the traffic. The hackers could manipulate the communication and hear the secured communication traffic. Further, the client initiated traffic could be redirected for cyber crimes like financial frauds and malware infection.
TLS was introduced taking view of security risks associated with SSL protocol. Below are the 4 versions TLS has gone through since its inception by IETF (The Internet Engineering Task Force) –
- TLS v1.0
- TLS v1.1
- TLS v1.2
- TLS v1.3
TLSv1.0 had some security weaknesses which could put financial transaction at risk and hence had to be stopped by 2018 by websites which were using credit cards or services used by US Government.
TLS 1.3 has made significant improvements compared to its predecessors and at present major players around the internet are pushing for its proliferation.
TLS 1.3 is currently the most up-to-date version of the protocol and is quickly taking the place of the standard encryption protocol for the web. The National Institute of Standards in Technology (NIST) mandates that all government TLS servers and clients must be configured with FIPS-based cipher suites and encourages agencies to design plans to aid them in transitioning to TLS 1.3 no later than January 1, 2024.
Most present day web browsers don’t support SSL 2.0 and SSL 3.0 now. Including Google Chrome, other major browsers have already or planning to shortly stop supporting TLS 1.0 and TLS 1.1.
Here is the chronological history of the two types of protocols:
Is TLS Replacing SSL?
It is true that TLS is taking the place of SSL. As was discussed above, the older versions of SSL have been largely considered unsafe because of the security risks associated with them. Due to this, SSL cannot be considered a totally secure protocol in the present time and beyond.
Comparison Table: SSL vs TLS
Now that we understand the SSL and TLS working and some historical events, lets illustrate difference between both protocols is below table: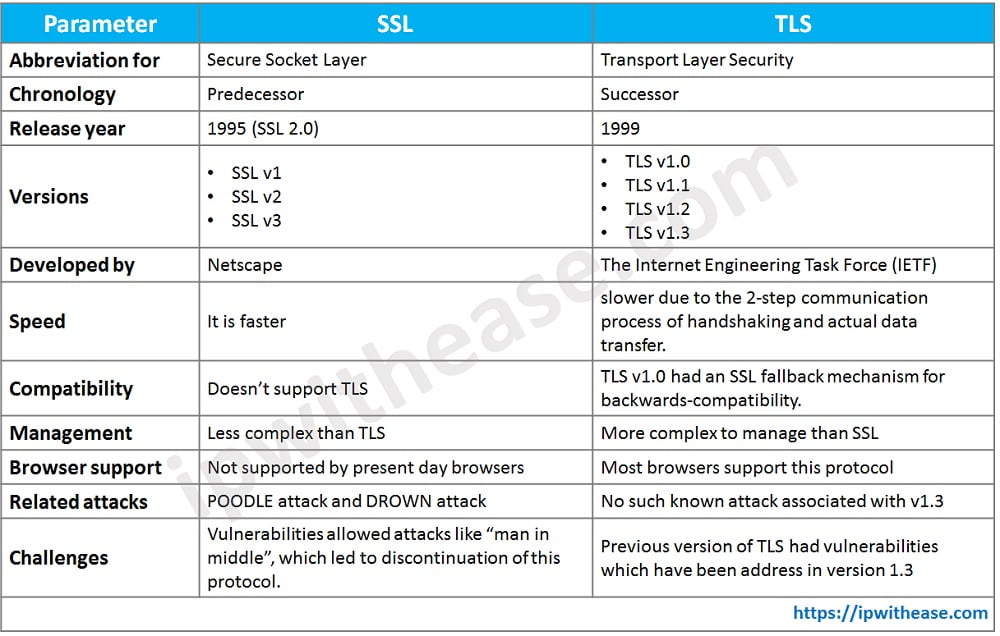
Final Words
TLS and SSL are protocols that ensure the safety of data that is transmitted over the internet. SSL is the more commonly used term, even though all public versions of it have been outdated for a while. Installing a certificate on the server is necessary in order to use either of these protocols, and they are typically referred to as “SSL certificates”. Both SSL and TLS protocols are compatible with these certificates.
Continue Reading:
IPSEC vs SSL : Detailed Comparison
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj