Table of Contents
Introduction to VMware NSX-T Load Balancer
Load balancers are very important components of networks and required to distribute network traffic in multiple WAN links, virtual machines and servers to avoid overload of the network without using any routing protocols. Load balancers reside in front of systems to route requests from clients to optimize capacity, and speed. Load balancer ensures servers are not overloaded and traffic redirection happens when the server is down. Cloud load balancers performs distribution of network load and routes client requests across servers to ensure load balancing and availability.
Today we look more in detail about VMware NSX-T load balancer, its components, architecture, features and deployment modes.
What is VMware NSX-T Load Balancer?
The NSX-T is a logical load balancer for data centers with high availability service for applications and used for distribution of network traffic among multiple servers.

- The load balancer performs distribution of incoming service requests between multiple servers ensuring load distribution in a transparent manner to users.
- It helps to optimize resource utilization, throughput maximization, response time optimization and minimization, and balance load to overcome issues of overload.
- Virtual IP addresses can be mapped to a pool of virtual servers to achieve load balancing.
- The load balancer accepts variety traffic be it UDP, TCP, HTTP or HTTPS requests on virtual IP addresses and decides which server from the pool will be chosen to service the request.
Related: VMWare NSX-T vs NSX-v: Comprehensive Comparison
Let’s look at various components of load balancer in detail.
VMware NSX-T Load Balancer Components
Load balancer components are
- virtual machines
- server pools and
- health check monitors
Load balancer is connected to a logical router (Tier 1). The load balancer can host single or multiple servers.
- A virtual server is a unique combination of IP address, pool and protocol and acts as an abstract of application service.
- Virtual machines are part of single or multiple server pools.
- Server pool comprises a group of servers which are individually pool members.
- Health check monitors are added to check the health status of servers in a pool. They ensure each server is running applications in the correct manner and to test this it uses a range of tests such as starting from basic test using ICMP to pattern matching in HTTPS queries.
- Pools specify monitors and a single pool can only use one health monitor only but same heath monitor can be used across multiple pools.

While configuring, load balancer size can be specified to determine the number of virtual machines, server pools, and pool members to be part of load balancer support capacity. It runs on a Tier 1 gateway in active-standby mode. The NSX-Edge nodes run on the gateway. We can call an API to obtain usage information of load balancer NSX edge node. If policy mode is used in configuration of load balancing use command.
GET /policy/api/v1/infra/lb-node-usage?node_path=<node-path>
If manager mode is used to configure load balancing use command:
GET /api/v1/loadbalancer/usage-per-node/<node-id>
The usage information comprises load balancer object (services, virtual servers, pools, and pool members) number that are configured on node.
Features of NSX-T Load Balancers
- TCP and UDP at Layer 4
- HTTP and HTTPS with rule support for load balancers at layer 7
- Static and dynamic server pools with NSGroup
- Persistence mode – Source IP and cookie
- Active health monitor – HTTP, HTTPS, TCP, UDP and ICMP; Passive health monitor
- Transparent, Automap and IP List in SNAT
- Supports and accepts HTTPS upgrade client requests in HTTP application profiles
NSX-T Deployment Modes
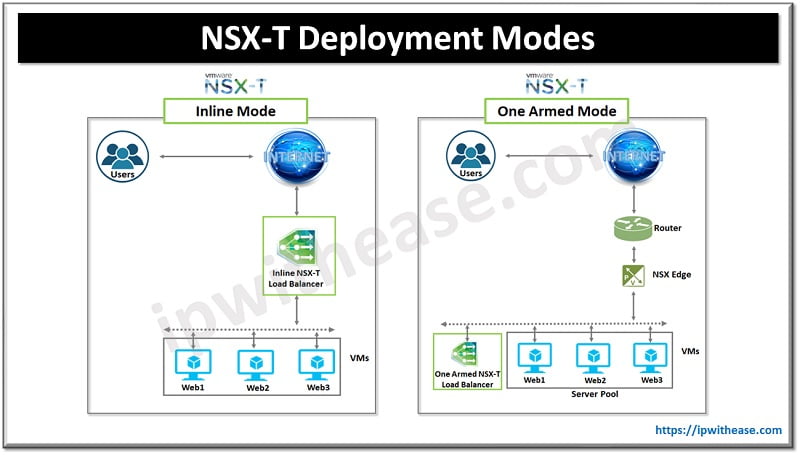
NSX-T can be deployed in In-line or one-arm mode.
- In Inline-mode, load balancer resides in the traffic path between client and server. Inline-mode not required SNAT if clients and servers are not connected to overlay segments in the same Tier 1 logical router.
- In one arm mode load balancer does not reside between client and server traffic path hence client and server can be anywhere. The load balancer uses SNAT to force return traffic to the router through load balancer for destined client. Virtual SNAT enablement required here.
Continue Reading:
ESX vs NSX: Detailed Comparison
Cisco ACI benefit over VMware NSX
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj