Network Connectivity: VPN vs ZTNA
Network connectivity and its means are there for ages. While VPNs provided remote users a secure way of connecting over public networks for many years, recently a new concept of Zero trust networks emerged in the age of cloud computing and questions started arising which is better a VPN an age oldest trusted way to connect to networks or newly found Zero trust network access.
Which one should we opt for to have better security since more and more workforce is working remotely or in hybrid mode and cyber attacks are on rise?
Today we look more in detail about two most popular terminologies related to network connectivity – VPNs or Virtual private networks and ZTNA or Zero trust network access, its key features, differences, advantages , limitations and use cases.
What is VPN?
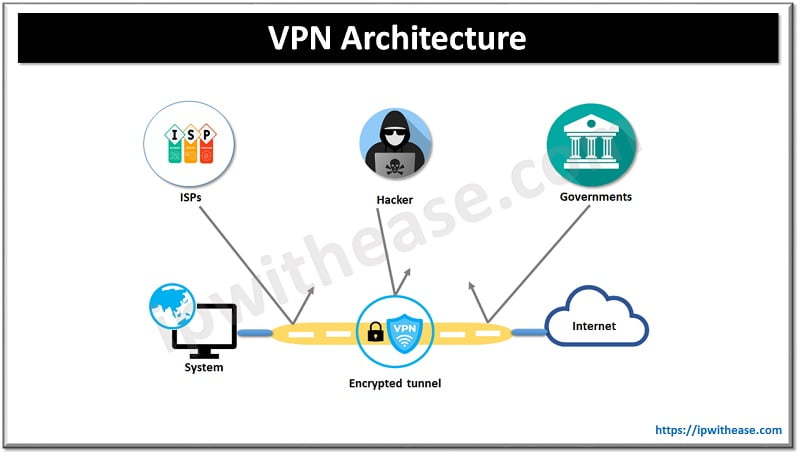
VPNs were introduced 30 years back. Legacy VPNs provide secure remote access to the corporate network through a point-to-point connection by creating an encrypted ‘tunnel’ through which IP traffic was flown. VPNs gave users within the organization access to the entire internal network so they can access company resources. Users are not restricted to specific network resources.
Limitations:
VPN’s one of the weakest points of failure lies with:
- Weaker identity access and credentials management.
- There is no segmentation, control or audit.
- VPNs were never meant to handle dynamically expanding networks because of which they are not meant to handle dynamic scaling of users and network locations and effectively manage hybrid and cloud-based computing architectures.
Features of VPN
- VPNs offer secure ‘tunnels’ over public networks to securely transmit network traffic
- VPNs prevent web browsers and others from accessing your private connection and help to keep information anonymous and secure.
- VPNs are cheaper alternative to expensive lease lines
- Let you escape data throttling usually imposed by ISPs
What is ZTNA?
Zero trust network access is a comparatively new concept which grants access to corporate resources based on the principle of zero trust, or least privilege. Users are granted access to what they actually need to access and where they need it as per their role.
Edge over VPN:
ZTNA addresses traditional VPN limitations and provides a
- flexible cloud-based platform,
- device and application configurability along with accessibility,
- improved security,
- privacy and granular user access control and analytics
They offer a 360-degree view of access and security. Reduction in attack surface for exposed hosts to help to reduce data breaches and loss of data, system and application vulnerabilities, advanced persistent threats (APTs), denial of service attacks, account hijacking and malicious insiders.
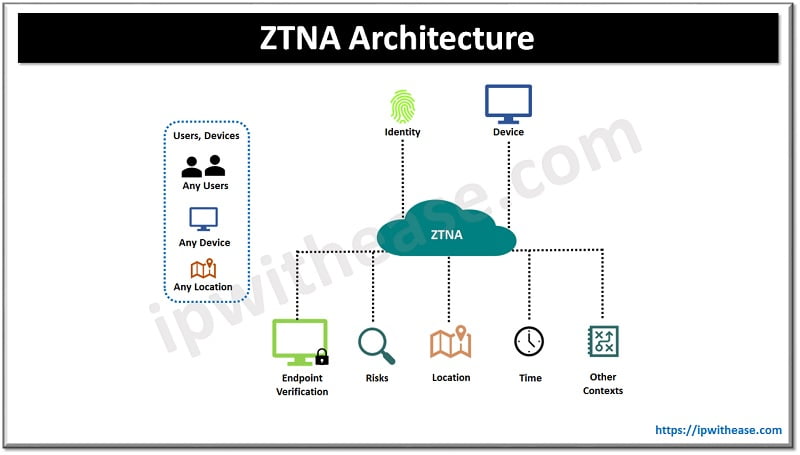
Features of ZTNA
- Offers single dashboard for managing network access, and security
- All access rules managed in a single location to avoid human error and gap in configuration
- Secure the real perimeter of the organization, not just physical infrastructure. Secures cloud perimeter which includes both remote users and cloud resources
- Allows network to expand with the organization
- Individual authorization of each access request helps to contain malicious users to move laterally across the network
- Seamless integration with identity provided and integrated multi factor authentication
- Ability to ensure all devices connected to VPN are authenticated and have correct device posture
- Comply with international standards like SOC 2 type 2 and ISO standards
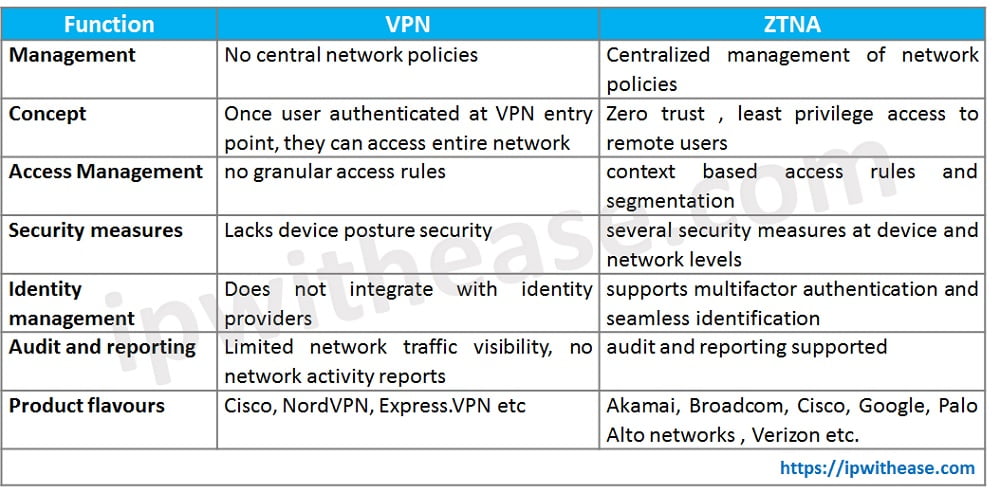
Comparison Table: VPN vs ZTNA
Below table summarizes the points of comparison between the VPNs or Virtual private networks and ZTNA and would be helpful in deciding to chose the right secure remote access for the corporate network as per the requirements. Let’s explore VPN vs ZTNA:
Quick Facts !
As per Gartner prediction 60% of enterprises shall phase out VPN in favour of ZTNA by year 2023.
Continue Reading:
What is ZTNA (Zero Trust Network Access)
Microsegmentation vs Zero trust
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj