With the advent of cloud computing and virtualization of servers in data centers there is a dramatic increase in flexibility and agility. Network virtualization and decoupling physical and virtual networks facilitate ease of management, automation, and orchestration. Segmentation of networks helps to resolve the issue of scalability and solves the limitation of virtual LANs (VLANs).
VXLAN or Virtual Extensible LANs helps to create extensive network segmentation thus enabling cloud providers to support a large number of tenants unlike traditional layer 2 network which is limited by its own boundaries and enforce creation of large and stretched layer 2 domains.
Today we look more in detail about VTEPs (VXLAN tunnel endpoints) and VNI (VXLAN Network identifier), how it works in a VXLAN environment, its features etc.
What are VTEPs (VXLAN Tunnel EndPoints)?
VTEPs (VXLAN tunnel endpoints) provide connectivity between overlay and underlay networks and are responsible for frame encapsulation into VXLAN packets to transport them across IP networks (underlay) and perform de-encapsulation once packet leaves VXLAN channel. The underlay network is not aware of VXLAN, for him VXLAN packet is just like any other normal packet.
VTEPs (VXLAN tunnel endpoints) can be hardware based (Cisco Nexus 9000 switch series) or software based (VXLAN capable hypervisor switch in hypervisor host).
VTEPs (VXLAN tunnel endpoints) have two interfaces:
- Local LAN interface – to give local communication by bridging endpoints connected to VTEPs
- IP interface – to connect the underlay layer 3 network also known as transport network. The IP address bind to the IP interface helps to uniquely identify VTEP in the network.
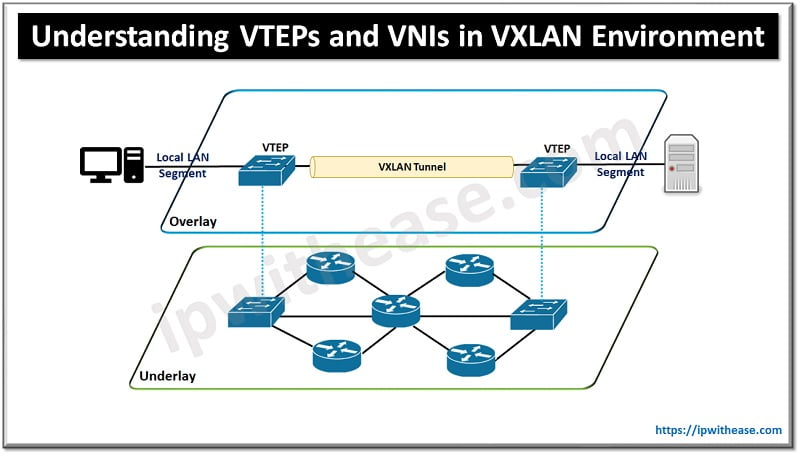
VTEPs (VXLAN tunnel endpoints) use an IP interface to learn about remote VTEPs (VXLAN tunnel endpoints) within its VXLAN segments and remote MAC address to VTEPs (VXLAN tunnel endpoints) mapping.
As overlay and underlay networks are independent of each other. Overlay networks are virtual and require an underlay network to function; however changes made in an overlay network do not impact the underlay network. Links can be added/removed in the underlay network as long as destination is reachable by routing protocol overlay network remains unchanged.
Encapsulation and decapsulation of VXLAN traffic
Encapsulation and decapsulation of VXLAN traffic done by VTEPs by adding additional fields such as:
- External MAC address (tunnel endpoint VTEP destination media access control address)
- External source MAC address (Tunnel VTEP source Mac address)
- External destination IP address (tunnel endpoint VTEP destination IP address)
- External source IP address (Tunnel VTEP source IP address)
- External UDP header (UDP port: 4789)
What is a VXLAN Network Identifier (VNI)?
The VXLAN Network Identifier (VNI) is meant to identify a specific virtual network in a data plane and performs a function similar to a VLAN ID in regular networks. VNI uses 24-bit and can create 16,777,215 (16 million) VXLANs. Which is much higher as compared to 12-bit VLAN ID which can only create 4096 VLANs. Two main VNI scopes are:
- VNIs (network wide scope) – same value is used across for identification of layer 3 virtual network on all network edge devices. This is ideally suited for data centers where central orchestration systems are used to auto provision networks. Having similar VNI makes ease of operations and simplification of requirements for network edge devices (physical and virtual).
- VNIs (Locally assigned) – As per RFC 4364 an alternate approach is supported. Local significance for network edge devices for the identifier to allow seamless stitching together to a VPN which spans across IP based overlay networks and MPLS VPN.
VXLAN Features
- VXLAN acts as extension for VLAN (layer 2) and extend layer 2 segments so tenant workload can be distributed across physical pods in data centers.
- VXLAN provides 24-bit segment ID referred as VXLAN network identifier (VNID) to enable 16 million VXLAN segments.
- VXLAN packets transmission happens through underlay network based on layer 3 header and it takes advantage of layer 3 routing, ECMP routing and all other available routing protocols to use all paths.
Continue Reading:
NVGRE vs VXLAN: Detailed Comparison
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj