Table of Contents
Insider threats represent one of the most insidious dangers to an organisation’s cybersecurity framework. These threats originate from individuals within the organisation, such as employees, contractors, or business associates, who have access to critical systems and data. Insider threats can be intentional, involving malicious actions such as data theft or sabotage, or unintentional, arising from negligence or human error. Whatever their source, they’re also becoming increasingly common—Cybersecurity Insiders’ Insider Threat Report 2023, for instance, stated that 74% of organisations worldwide had at least a moderate measure of vulnerability to insider threats.
How to Address Insider Threats
The public sector, with its vast repositories of sensitive information and critical infrastructure, is particularly vulnerable to these threats. Government agencies must, therefore, be proactive in identifying and mitigating these internal liabilities to safeguard national security and public trust. The Singapore government, in particular, stands as a global leader in cyber defence and has implemented a range of robust measures to address insider threats within its public sector cybersecurity frameworks. These initiatives not only protect Singapore’s digital infrastructure but also serve as models for other nations striving to enhance their cybersecurity defences.
This feature aims to lay out key strategies for addressing insider threats within the public sector as part of a broader cyber defence strategy. It will also substantiate some of these strategies with examples of initiatives that have contributed to the overall strengthening of cyber defence in Singapore, in the interest of demonstrating how government agencies anywhere in the world can achieve effective insider threat mitigation.

Implement Strict Access Controls
One fundamental cybersecurity principle is that only authorized personnel should have access to sensitive information. To start with, organisations must enforce the principle of least privilege, where employees are granted access only to the data and systems necessary for their roles. Regular reviews and updates of all access permissions are crucial to account for changing roles and responsibilities. In addition, the use of multi-factor authentication (MFA) can make it difficult for unauthorised individuals to gain access by adding an additional layer of security that users must clear.
Related: Strategies to Safeguard Your Business From Cyber Fraud
Communicate and Enforce Cybersecurity Policies
Clear and consistent communication of cybersecurity policies is essential for ensuring that all employees understand their roles and responsibilities in maintaining security. These policies should be well-documented, regularly updated, and easily accessible. Enforcement of these policies, coupled with regular reminders and updates, can act as a deterrent to potential insider threats. Moreover, having strict consequences for policy violations underscores the seriousness with which the organisation views cybersecurity.
Conduct Regular Cybersecurity Audits
Frequent cybersecurity audits are essential for identifying vulnerabilities and maintaining compliance with security protocols. These audits involve a thorough examination of systems, networks and processes to detect any weaknesses that insider threats could exploit. Both automated tools and manual reviews play a role in conducting effective audits and producing a comprehensive assessment of the security landscape.
Singapore’s Cyber Security Agency (CSA) has established the Cybersecurity Labelling Scheme (CLS), which assesses the security levels of Internet of Things (IoT) devices and awards labels based on their security features. While the CLS focuses on IoT devices, its rigorous auditing principles highlight the importance of regular assessments in maintaining robust cybersecurity practices. By adopting similar audit practices, government agencies can maintain a high level of security and swiftly address any detected vulnerabilities.
Establish Comprehensive Security Training & Awareness Programmes
Well-informed and vigilant employees are every organization’s first line of defence against cyber threats. Comprehensive security training and awareness programmes are crucial for educating staff about the various threats they might encounter, including insider threats. Regular training sessions should cover the latest cybersecurity threats, proper data handling procedures, and the importance of adhering to security policies. Fostering a culture of security awareness in this way can help organizations significantly reduce the risk of both intentional and unintentional insider threats.
In Singapore, the SG Cyber Safe Programme spearheaded by the Cyber Security Agency (CSA) serves as a prime example of such an initiative. This programme aims to educate the public and organisations on cybersecurity best practices and tailors its content to different segments, including government employees. Highlights of the programme include targeted training sessions, resources for improving cyber hygiene, and initiatives to raise overall cybersecurity awareness across various sectors.
Deploy Technological Solutions
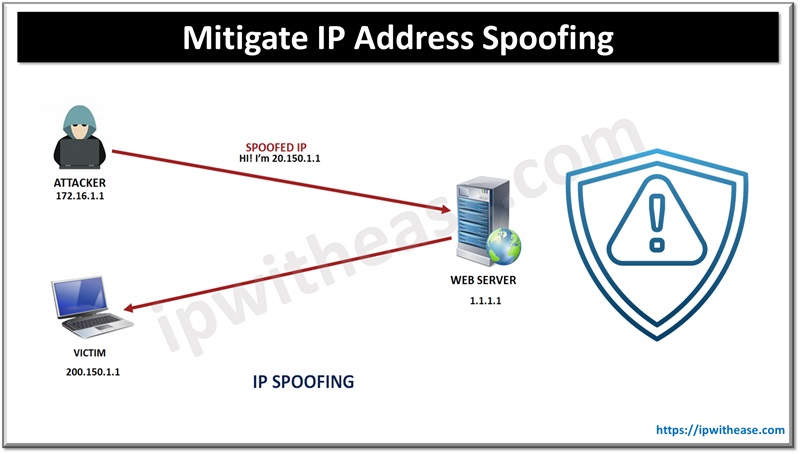
Advanced technological solutions play a vital role in detecting and preventing insider threats. Tools such as continuous monitoring systems, Data Loss Prevention (DLP) systems and User and Entity Behavior Analytics (UEBA) can help identify abnormal behaviour patterns that may indicate an insider threat. These technologies enable organisations to detect potential attacks and respond to these in real time, before they escalate into serious security breaches.
Singapore’s Government Cyber Security Operations Centre (GCSOC) exemplifies the effective deployment of technological tools for public sector cybersecurity. Commissioned by GovTech in 2022, the GCSOC centralises cybersecurity operations across government agencies and leverages artificial intelligence and machine learning to enhance security analytics. Over the course of its tenure so far, GCSOC has managed to achieve improved detection coverage, proactive threat hunting, and faster response times—all of which distinguish it as a cornerstone of Singapore’s effort to safeguard its public sector infrastructure.
Mitigating insider threats within government cybersecurity frameworks is a complex but essential task—and moreover, one that is entirely achievable with the technologies and methodologies currently available. Other nations can learn from Singapore’s comprehensive approach to enhance their own cybersecurity measures. Ultimately, a proactive and well-rounded strategy is crucial for protecting sensitive information and maintaining public trust in the digital age.
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.