Table of Contents
Introduction to Packet Forwarding Order of Operations in SD WAN
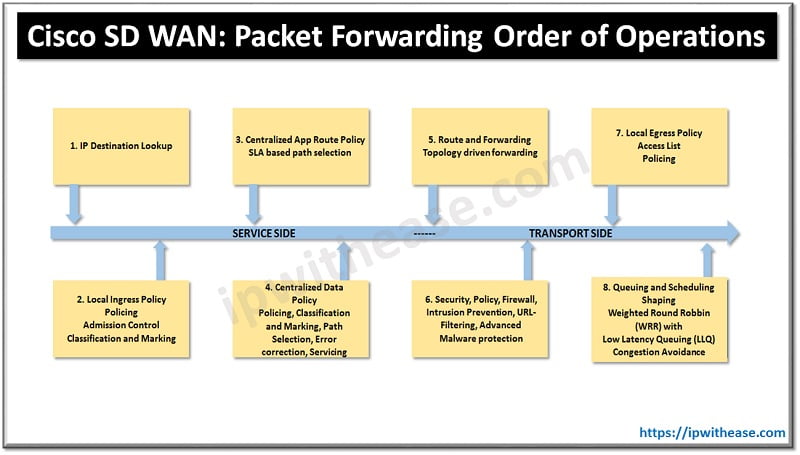
In SDWAN, As multiple types of policies can be applied to a given site and affect the forwarding of a single flow, it is important to understand the order of operations in which these policies are applied and evaluated, and how they work together.
Firstly, as control policies do not directly affect the data plane, they are processed independently of data plane policies. Control policies instead impact the routing information that the data plane is built upon and, in this manner, they are able to impact the forwarding of traffic. As control policies filter, manipulate, summarize, or restrict the advertisement of a specific routing prefix or TLOC, WAN Edge will have altered control plane information and will build its forwarding plane from this altered control plane information.
Steps: Packet Forwarding Order of Operations
The following steps are evaluated sequentially when forwarding a packet (order of operations) through a WAN edge router:
- IP Destination Lookup: The first step in the packet-forwarding process is to perform a routing lookup on the destination IP of the packet in the routing table. This information is then used to inform the rest of the forwarding decisions that are made as the packet is processed through the WAN Edge router.
- Ingress Interface ACL: Localized policy can be used to create ACLs and tie them to interface templates. Interface ACLs can be used for packet filtering, policing, and QoS marking or remarking. If a packet is denied by the ingress ACL, it is dropped at this point and is not processed any further.
- Application-Aware Routing: The Application-Aware Routing policy is evaluated after the forwarding decision has been made based on the routing table. It is important to note that an Application-Aware Routing policy can only make distinctions between equal paths in the routing table. If the routes for a destination’s multiple next-hop addresses are not equal-cost paths in the routing table, then the Application-Aware Routing policy will have no effect, and the flow will follow the most preferred path based on the routing table.
- Centralized Data Policy: The centralized data policy is evaluated after the Application-Aware Routing policy and is able to override the Application-Aware Routing forwarding decision.
- Routing and Forwarding: Routing lookups are now performed to determine the correct output interfaces so that processing can be continued there.
- Security Policy: If security policies are configured, they are processed in the following order: Firewall, Intrusion Prevention, URL-Filtering, and finally Advanced Malware Protection.
- Encapsulation and Encryption: As packets are prepared to be forwarded across the fabric, the necessary VPN labels and tunnel encapsulations are performed.
- Egress Interface ACL: As with ingress ACLs, local policy is able to create ACLs that are applied on egress as well. If the traffic is denied or manipulated by the egress ACL, those changes will take effect before the packet is forwarded.
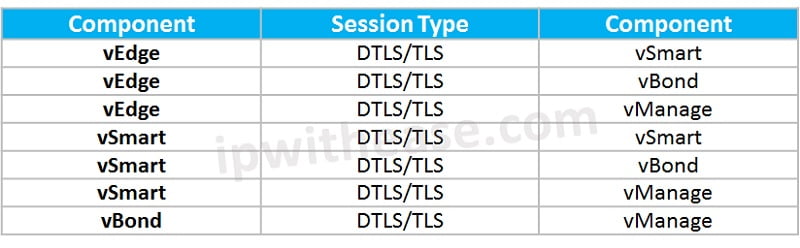
Traffic Used Pattern of Control Plane between the four components
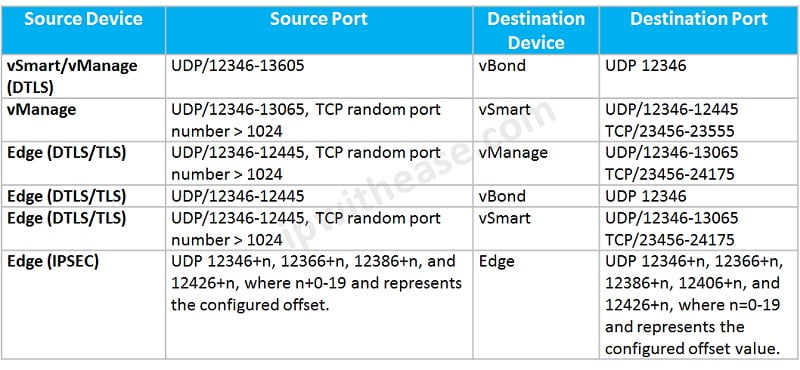
DTLS is the default using port 12346 can increment by 20 for 4 times only but vBond use 12346 only. Control plane secure session formed between SD-WAN components: –
- Digital certificates are used for authentication.
- AES-256 encryption algorithm provides encryption
- SHA-1 or SHA-2 is responsible for ensuring integrity between components.
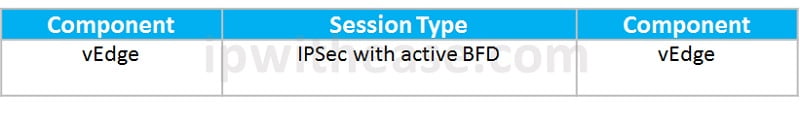
Data Plane Traffic used between: where BFD session is mandatory to have a successful IPSec session. [BFD is enabled by default].
SD-WAN Firewall Traffic Requirement
Continue Reading:
Cisco SD-WAN Policy: Localized Policy
Cisco SD-WAN Policy: Centralized Policy
Cisco SD-WAN Security: Application Aware Enterprise Firewall
Are you preparing for your next interview?
Please check our e-store for e-book on Cisco SD WAN Viptela Interview Q&A . All the e-books are in easy to understand PDF Format, explained with relevant Diagrams (where required) for better ease of understanding.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj