In today’s interconnected world, the threat landscape is growing at an alarming rate, posing significant challenges to individuals, organizations, and governments. Cyber security has become a top priority as cybercriminals continuously devise new techniques to exploit vulnerabilities and gain unauthorized access to sensitive information.
This article discovers the emerging cyber security challenges that we must be aware of to protect ourselves and our digital assets.
Understanding Cyber Security
Understanding cyber security is vital in today’s interconnected world. It refers to the practice of protecting computers, networks, and data from unauthorized access and cyber threats. Cyber security encompasses a range of measures, including network security, data encryption, incident response, and security awareness training. It involves staying updated on the latest threats and vulnerabilities, implementing robust security controls, and fostering a culture of security within organizations.
To understand cyber security in-depth, individuals can explore various resources such as cyber security courses, books, and industry publications. These resources provide insights into the common types of cyber threats, such as malware, phishing, and ransomware, and offer guidance on how to prevent and mitigate these risks.
Learning about emerging technologies and trends in the field, such as artificial intelligence and blockchain, can help individuals stay ahead of evolving threats. By understanding the principles and best practices of cyber security, individuals can play an active role in protecting their personal information, as well as contribute to a more secure digital environment for organizations and society as a whole.
The Rise of Cyber Threats
With the rapid technological advancements, cyber threats have evolved and become more sophisticated. Hackers and malicious actors are constantly adapting their tactics to exploit weaknesses in systems and networks. Recent high-profile cyber attacks, such as the ransomware attack on a major healthcare provider or the data breach affecting millions of social media users, highlight the scale and impact of these threats.
Emerging Cyber Security Challenges
Ransomware Attacks
Ransomware attacks have become increasingly prevalent, causing significant disruption and financial losses for individuals and organizations alike. These attacks involve malicious software that encrypts files and demands a ransom to restore access. Notable incidents like the WannaCry attack and the Colonial Pipeline ransomware incident have demonstrated the devastating consequences of such attacks. Preventing and mitigating ransomware requires robust backup strategies, regular software updates, and user education on phishing and suspicious email attachments.
IoT Vulnerabilities
The advancement and widespread of Internet of Things (IoT) devices present new security challenges. IoT devices, like smart home appliances and industrial sensors, often lack proper security measures, making them susceptible to exploitation. Inadequately secured IoT devices can be used as entry points into networks, leading to data breaches or even physical harm. To address IoT vulnerabilities, manufacturers and users must prioritize security measures, such as strong passwords, regular firmware updates, and network segmentation.
Cloud Security Concerns
As organizations increasingly rely on cloud services, securing cloud environments has become critical. Cloud misconfigurations, data breaches, and unauthorized access incidents have made headlines in recent years, highlighting the need for robust cloud security measures. Organizations must implement strong access controls, encryption protocols, and regular vulnerability assessments to protect their data in the cloud.
Social Engineering and Phishing Attacks
Social engineering remains a prevalent tactic that cybercriminals use to trick individuals into giving up detailed sensitive information or installing malware. Phishing attacks, in which fraudulent emails or websites mimic legitimate ones, have become highly sophisticated and difficult to detect. Cyber security awareness and training programs are essential to educate users about the risks and teach them how to recognize and respond to these threats effectively.
Insider Threats
Insider threats, whether unintentional or malicious, pose a significant risk to organizations. Employees or contractors with authorized access can exploit their privileges, intentionally or inadvertently, compromising data security. Detecting and mitigating insider threats requires a combination of technical controls, employee monitoring, and a strong security culture that encourages reporting suspicious activities.
Addressing Emerging Cyber Security Challenges
Collaboration and Information Sharing
To combat the ever-evolving cyber threats, collaboration and information sharing among industry, government, and academia are crucial. By pooling resources and sharing threat intelligence, organizations can stay one step ahead of cybercriminals. Initiatives such as public-private partnerships and industry consortiums have proven effective in fostering collaboration and strengthening defenses.
Proactive Defense Strategies
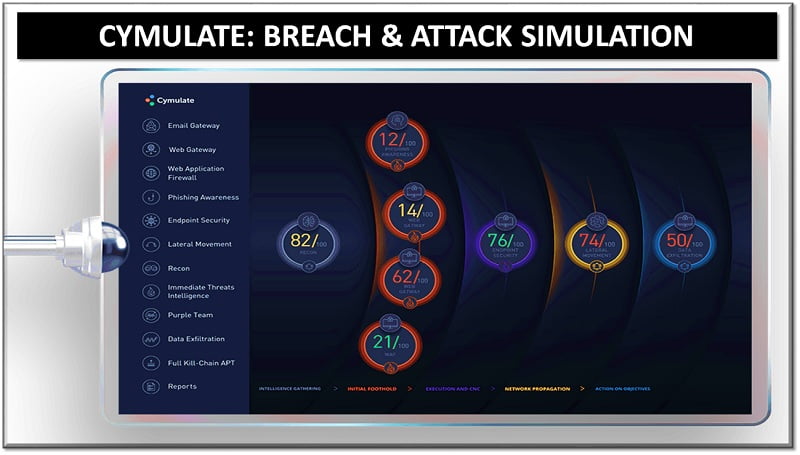
A proactive approach is essential in today’s threat landscape. Implementing robust security measures, employing defense-in-depth strategies, and continuously monitoring systems are critical components of proactive defense. Advanced technologies like artificial intelligence and machine learning can assist in threat detection and response, enabling organizations to identify and mitigate potential attacks more effectively.
Security Awareness and Training
People remain a critical line of defense in cyber security. Building a security-conscious culture and providing regular security awareness training is vital to empower individuals to recognize and respond to emerging cyber security threats. Training should cover topics such as password hygiene, safe browsing habits, and the identification of suspicious emails or messages. By imparting individuals the knowledge and skills to navigate the digital landscape securely, organizations can significantly reduce the risk of successful cyber attacks.
Regular Vulnerability Assessments and Patch Management
Regular vulnerability assessments and patch management are crucial for maintaining strong cyber security defenses. Organizations should implement a robust process to identify and address vulnerabilities in their systems and software promptly. By staying updated with security patches and fixes, organizations can prevent the exploitation of known vulnerabilities by threat actors.
Incident Response and Business Continuity Planning
In the occurrence of a cyber security incident, organizations must have well-defined incident response plans and business continuity strategies in place. These plans outline the necessary steps to contain and mitigate the impact of an attack, as well as the process for restoring operations and recovering compromised data. Regular testing and simulation exercises can help organizations refine their incident response capabilities and ensure readiness in the face of emerging threats.
Cyber Security Jobs
As the threat landscape continues to expand and evolve, new and emerging cyber security challenges create a demand for specialized skills and expertise. This has led to the emergence of various job roles dedicated to tackling these challenges.
Here are some of the emerging jobs in the field of cyber security:
- Threat Intelligence Analyst: These professionals specialize in monitoring and analyzing potential threats and vulnerabilities to anticipate and prevent cyber attacks. They gather intelligence from various sources, including dark web monitoring, and provide timely insights to help organizations strengthen their security posture.
- Incident Responder: With the increasing frequency and complexity of cyber attacks, incident responders play a crucial role in detecting, analyzing, and responding to security incidents. They investigate breaches, identify the root causes, contain the impact, and implement measures to prevent future incidents.
- Security Automation Engineer: As organizations strive to enhance their security operations and response capabilities, security automation engineers design and implement automated systems to streamline and optimize security processes. They develop scripts, workflows, and tools to automate tasks like threat hunting, incident response, and vulnerability management.
- Cloud Security Architect: With the growing adoption of cloud computing, cloud security architects design and implement secure cloud environments. They assess cloud architecture, develop security policies and controls, and ensure compliance with industry standards. They also provide guidance on best practices for securing cloud-based infrastructure and data.
- Data Privacy Officer: As data protection and privacy regulations become more stringent, organizations require professionals who specialize in managing privacy risks and ensuring compliance. Data privacy officers develop and enforce privacy policies, conduct privacy impact assessments, and provide guidance on data handling practices.
- IoT Security Specialist: With the proliferation of Internet of Things (IoT) devices, there is a need for experts who can address the unique security challenges associated with IoT deployments. IoT security specialists focus on securing connected devices, implementing encryption and authentication mechanisms, and mitigating vulnerabilities in IoT ecosystems.
- Cyber Security Consultant: As organizations seek external expertise to assess their security posture and develop robust strategies, cyber security consultants provide advisory services. They conduct risk assessments, design security frameworks, recommend solutions, and help organizations navigate complex compliance requirements.
Conclusion
As the threat landscape continues to evolve bigger, it is essential for individuals and organizations to stay vigilant and adapt their cyber security strategies accordingly. By understanding and addressing emerging cyber security challenges, we can better protect our digital assets, sensitive information, and critical infrastructure. By embracing proactive defense measures, fostering a culture of security awareness, and leveraging collaboration and technological advancements, we can build a stronger defense against the ever-changing threat landscape. Together, we can navigate the complexities of the digital age with confidence and resilience.
Continue Reading:
5 Types of Cyberattacks and How to Protect Your Business Data
Network Vulnerabilities and the OSI Model
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.