Table of Contents
In this blog, we will discuss the steps to configure SSH version 2 on Cisco router along with the verification commands.
The SSH protocol (Secure Shell) is a method for secure remote login from one device to other. SSH provides a secure channel over an unsecured network in a client-server architecture, connecting an SSH client application with an SSH server. As discussed in another blog, SSH has two versions, namely, SSH version 1 and SSH version 2 –
SSH Version 1
SSH v1 (Secure Shell) provides an encrypted channel to users for logging into remote device. It provides strong host-to-host and user authentication. It also provides secure encrypted communications over the Internet.
SSH Version 2
On the contrary, SSH v2 is a much more secured, an efficient version of SSH that includes SFTP, which is functionally similar to FTP with addition of SSH v2 encryption.
SSH works on port 22. It is a secure alternative to the non-protected login protocols (such as Telnet) and insecure file transfer methods (such as FTP).
Steps to Configure SSH
- Configure the router hostname using command “hostname”.
- Configure the domain name using command “ip domain-name”.
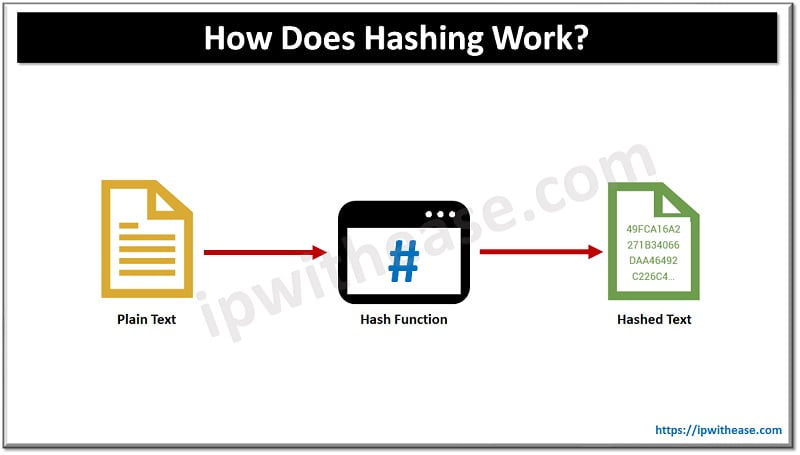
- Generate public and private keys using command “crypto key generate rsa”.
- Create a user in the local database using command “username…secret”.
- Allow only SSH access on VTY lines using command “transport input ssh”.
SSH Version 2 Configuration on a Cisco router IOS
Step 1
Configure Hostname and DNS Domain
hostname R1
aaa new-model
username Cisco password Cisco
ip domain-name Cisco.localStep 2
Generate RSA key to be used.
ip ssh rsa keypair-name sshkeyEnables the SSH server for local and remote authentication on the router
For SSH Version 2, the modulus size must be at least 768 bits.
crypto key generate rsa usage-keys label sshkey modulus 768Configures SSH control variables on the Router.
ip ssh timeout 120Configure SSH version 2 (This will disable SSH version 1)
ip ssh version 2Step 3
Enable SSH transport support for the virtual type terminal (vty)
line vty 0 4
transport input SSHCommands to Verify SSH Configuration
show ssh
how ip ssh
debug ip sshSSH Version 1 vs SSH Version 2
| Feature | SSH-1 | SSH-2 |
| Protocol Design | Simple, older protocol | More complex, newer protocol |
| Security | Known vulnerabilities, less secure | More secure, addresses SSH-1 vulnerabilities |
| Authentication Methods | RSA only | RSA, DSA, ECDSA, and ED25519 |
| Key Exchange Algorithms | Limited | Diffie-Hellman Group Exchange, ECDH |
| Encryption Algorithms | 3DES, Blowfish, DES | AES, 3DES, Blowfish, others |
| Integrity Checking | CRC-32 | HMAC (SHA-1, MD5, etc.) |
| Compression | Not standardized | Standardized, optional |
| Forward Compatibility | Not forward-compatible | Designed with future compatibility in mind |
| Session Re-keying | Not supported | Supported |
| Multi-channel Support | Not supported | Supported |
| SFTP (File Transfer) | Limited, not standardized | Fully supported and standardized |
| Preferred Usage | Deprecated, should be avoided | Widely recommended and used |
SSH-2 is the preferred and recommended version due to its enhanced security features and improved functionality.
SSH Vulnerabilities
Despite being significantly more secure than SSH-1, SSH-2 is not immune to vulnerabilities. Here are some known vulnerabilities and security concerns associated with SSH-2:
- Weak or easily guessable passwords
- Man-in-the-Middle (MitM) Attacks
- Usage of deprecated or weak encryption algorithms and key exchange methods
- Poor management of SSH keys (e.g., not rotating keys, not properly securing private keys).
- Use of weak keys (e.g., RSA keys less than 2048 bits).
- Specific implementations of SSH-2 may contain bugs or flaws (e.g., OpenSSH, Dropbear, etc.).
- Timing attacks on encryption algorithms.
- Side-channel attacks targeting the SSH client or server’s computational processes.
- Brute Force and Dictionary Attacks: SSH servers exposed to the internet can be targeted for brute force attacks attempting to guess usernames and passwords.
- Protocol Downgrade Attacks: Attempting to downgrade the connection to a less secure version or cipher suite, though SSH-2 is generally resistant to this compared to SSH-1.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj