From your brand name and logo to your inventions and trade secrets, your business’s intellectual property can be the difference between success and failure.
While you can get legal protection for your intellectual property in the form of things like copyright, trademarks, and non-disclosure agreements, when your creative works are online, there is sure to be the risk of IP threats.

Three things you need to avoid
1. Casual Theft and Misuse
Your business probably uses the internet to promote and sell products or services and to enable collaboration between employees.
While the web has opened up a wealth of opportunities for businesses to collaborate and get their products seen, the internet does have its disadvantages.
When it comes to intellectual property like your brand name, logo, designs, and images, the last thing you want is for it to be stolen or misused.
Often, intellectual property is misused by individuals and small businesses who simply do not realize they are doing wrong. After all, we live in a culture of copying and pasting content online without giving it much thought.
You can make casual misusers think twice before they use your content by copyrighting and trademarking it.
When people see the © symbol or the ™ symbol, they know that the intellectual property has legal protection and that they could get into trouble for stealing or misusing the content.
So, to avoid people from causally using your intellectual property without your permission, simply protect it with copyright, trademarks, and patents.
Your first step in protecting your intellectual property should be to get advice from an experienced law firm like Heer Law.
Once your content is protected, in addition to using the copyright and trademark symbols, use notices and disclaimers to notify people of your legal rights and stop them from abusing your intellectual property online.
2. Intentional Theft by Cybercriminals
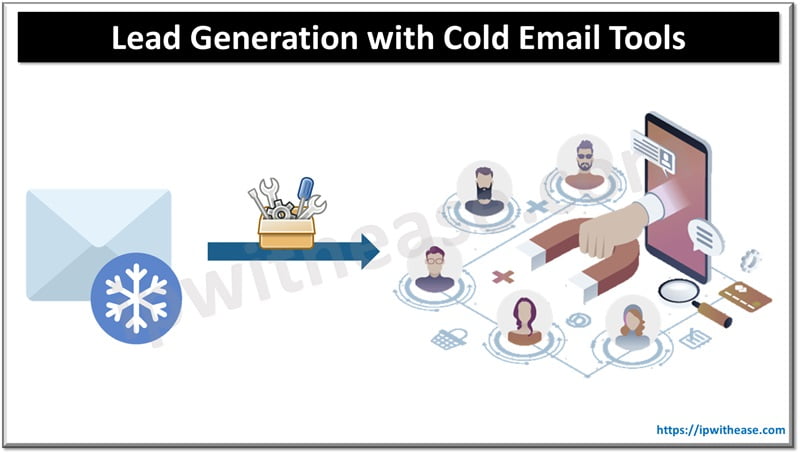
Legally protecting your intellectual property with things like copyright and trademarks can prevent law-abiding people from stealing or misusing your content, but of course, there are also lots of people who purposely steal intellectual property and do not care that they are doing so illegally.
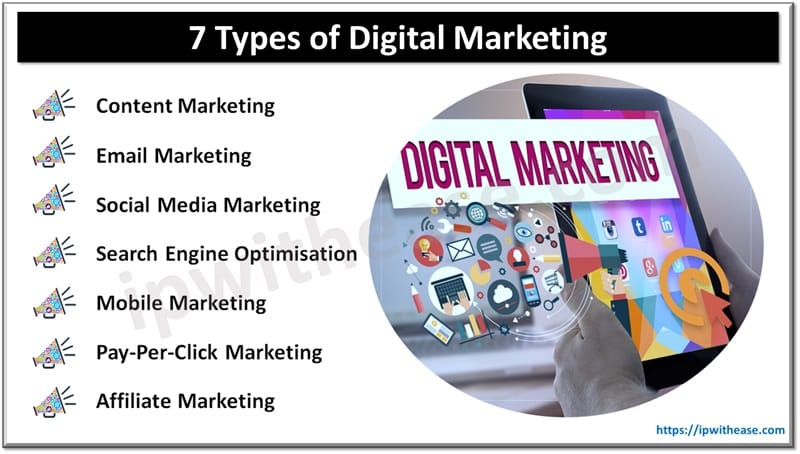
For example, cybercriminals often use fake social media accounts to mimic brands or imply an association with them.
A fake social media site could use your brand and intellectual property to do things like sell counterfeit goods or redirect traffic to illegitimate platforms that use tactics like phishing to steal people’s financial and personal information.
You can certainly help to prevent thieves from stealing your intellectual property by legally protecting it, but you will not always be able to stop it. Also, the more well-known your brand becomes, the more likely it is that cybercriminals will attempt to rip it off.
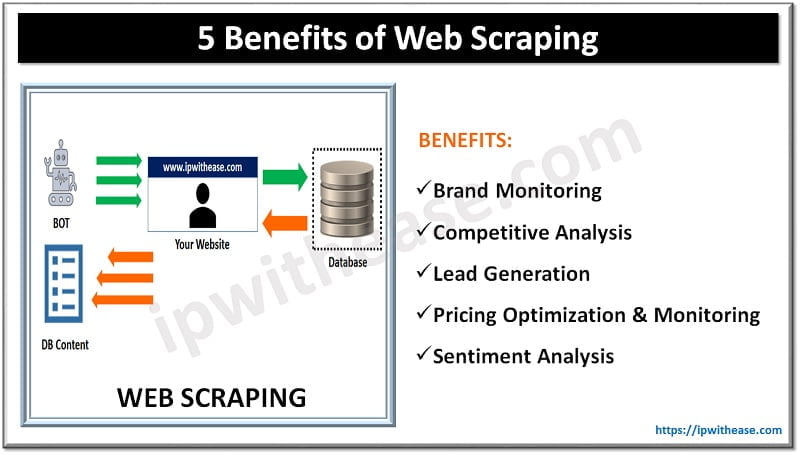
The important thing is to keep an eye on online fraudsters. Perform searches regularly to identify any misuses of your intellectual property. As long as you have legal protection like copyright and trademarks in place, you can then take steps against the perpetrators and protect your brand.
3. Intentional Theft by Insiders
The more employees you have and the more they work online, the greater your risk of intellectual property theft by insiders is.
While employee negligence that leads to intellectual property misuse should also be on your radar, it is intentional theft by people who work for or with your company that is the biggest threat.
Intentional theft by employees or contractors is often motivated by malice. It often occurs after an employee feels that he or she has been treated unfairly and blames the company. Basically, some employees want revenge. One way of them achieving that is to steal intellectual property.
For instance, an employee could steal the design for a new top-secret product that is protected by a non-disclosure agreement and give it to a competitor.
There are several ways of avoiding insider threats. You can use an email logging system that monitors all employees’ emails and sends alerts when messages are sent to suspicious addresses. You can also deploy specific security policies that limit access to files, use removable storage to protect sensitive information, and introduce hefty financial penalties for anyone who leaks your trade secrets.
Continue Reading:
Top 6 Business Cyber Security Tips: How To Protect Your Company
Whaling Phishing Attack – Cyber Security
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.