Table of Contents
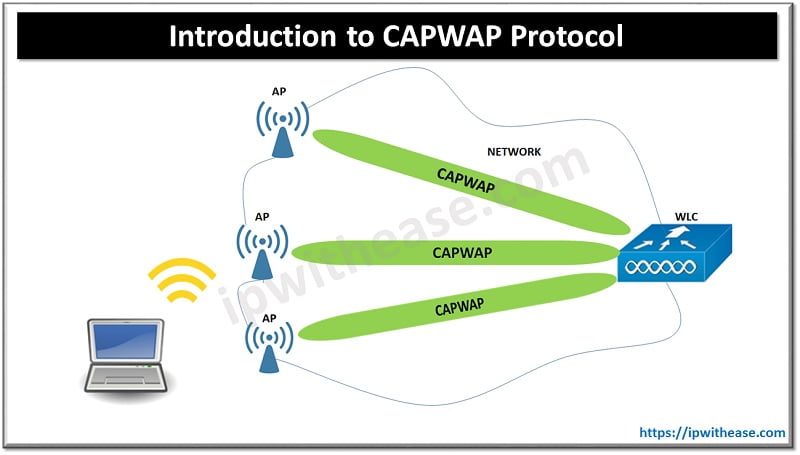
The full form of CAPWAP protocol is Control and Provisioning of Wireless Access Points protocol .
So, Control and Provisioning of Wireless Access Points protocol (CAPWAP) is a networking protocol that enables a central wireless Controller to manage a group of wireless access points. When the AP joins a WLC, a Control and Provisioning of Wireless Access Points protocol (CAPWAP) tunnel is formed between the two i.e. WLC and AP. All traffic generated from users is sent through the CAPWAP tunnel. It is not supported in layer 2 mode unlike LWAPP which is supported in both Layer 2 and Layer 3 mode.
Related – CAPWAP vs LWAPP
CAPWAP Messages
- “Data Messages” are encapsulated and forwarded frames from and to wireless clients. UDP port 5247 is used for data channel.
- “Control Messages” are management messages exchanged between the wireless LAN controller and the access point. UDP port 5246 is used for control channel.
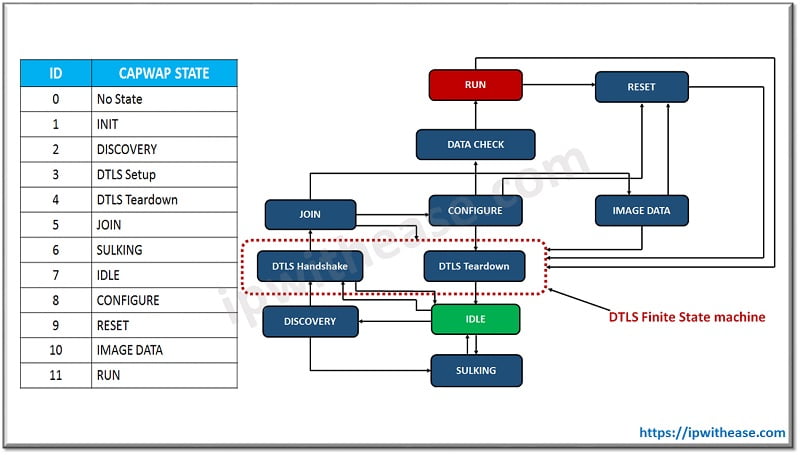
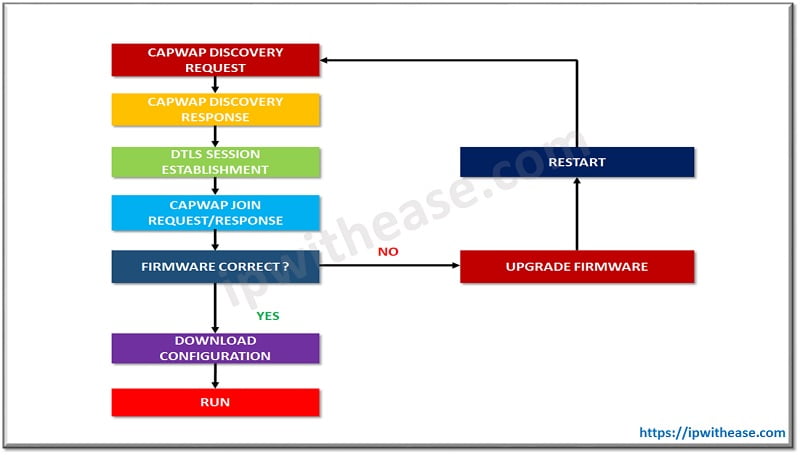
CAPWAP Protocol State Machine
Goals of CAPWAP
- CAPWAP enables a centralized management solution in a typical WLAN deployment.
- CAPWAP should make configuration of multiple hardware and ensure configurations are consistent across the network.
- CAPWAP monitors the status of both hardware and software configurations to ensure a properly operating network.
- To ensure that network security from 3rd party hardware such as rogue access points is being connected to the network.
WAP and WLC Communication
Below is step by step process of WAP to WLC communication –
- Discovery – New AP seeks out a controller with which to associate. This is accomplished by the AP sending broadcast Discovery Request. A WLC must respond with a Discovery Response. AP then joins to a controller.
- Image Download – Newly joined AP then may request a firmware update upon seeing the controller advertise a higher version of code. The AP then downloads the firmware, and once completed, enters the Reset state, and then attempts to re-join a controller.
- Configure – AP with an updated version of code may then request to be configured by the controller. The AP sends current configuration and the controller responds with an updated configuration. Once the AP has received the latest configuration from controller it may enter the Run state.
- Run – Both the controller and AP operates in the Run state. The AP forwards packet to the controller and maintains normal operation. They also exchange new key material and this encryption key is used to encrypt all further messages until a new key is requested.
Vendor
CAPWAP is approved by the IETF but has not seen very widespread deployment. Now vendors have started slowly migrating towards CAPWAP support. Some of vendors which have embraced CAPWAP protocol for its Wireless communication are –
- Trapeze Networks
- Cisco Systems
- Meru Networks
- Aruba Networks
Key Commands for CAPWAP configuration in Cisco
COMMANDS | DESCRIPTION |
| capwap ap | To configure the primary, secondary and tertiary controllers for the AP |
| capwap ap auth-token | To configure authentication token |
| capwap ap erase all | To erase CAPWAP configuration |
| capwap ap ethernet | To configure AP Ethernet parameters |
| capwap ap ethernet tag 2 | To configure Ethernet VLAN tagging on the AP |
| capwap ap hostname | To configure AP hostname |
| capwap ap ip | To configure static IP address and DNS for the CAPWAP AP |
| capwap ap lag | To configure CAPWAP lag |
| capwap ap mesh strict-wired-uplink | To configure the root access points (RAPs) to stay as persistent RAPs even if the wired uplink is lost, |
| capwap ap mode | To configure AP mode |
| capwap ap restart | To restart the CAPWAP protocol |
Conclusion
CAPWAP was developed by IETF. It is used for managing WAP by the WLC. CAPWAP forms tunnel between WAP and WLC to take control over WAP by WLC for
- Firmware upgrade
- Configuration
- Authentication
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj