Learning Management Systems (LMS) have become a part of training institutions worldwide. They empower educators to deliver content, interact with learners, and monitor their progress. However, as reliance on LMS software grows, safeguarding user data has become a concern. This blog post will delve into the security measures organizations must take during LMS software maintenance to effectively protect user data.
Security Measures in LMS Software
Regular Updates and Patches
One of the steps in securing LMS software maintenance is ensuring regular updates and prompt implementation of patches provided by the software vendor. These updates and patches address any vulnerabilities or weaknesses within the system, significantly reducing the risk of data breaches. Therefore, institutions must keep their LMS software current by applying these updates as they are made available, such as those available through Bridge training.
Robust Authentication and Access Controls
Another pivotal security measure in LMS software maintenance is implementing authentication protocols and access controls. Enforcing password policies, incorporating multi-factor authentication methods, and limiting access solely to authorized personnel institutions can substantially mitigate user data access risk.
In addition, role-based access controls guarantee that users get access to the information they need, providing a layer of security for sensitive data.
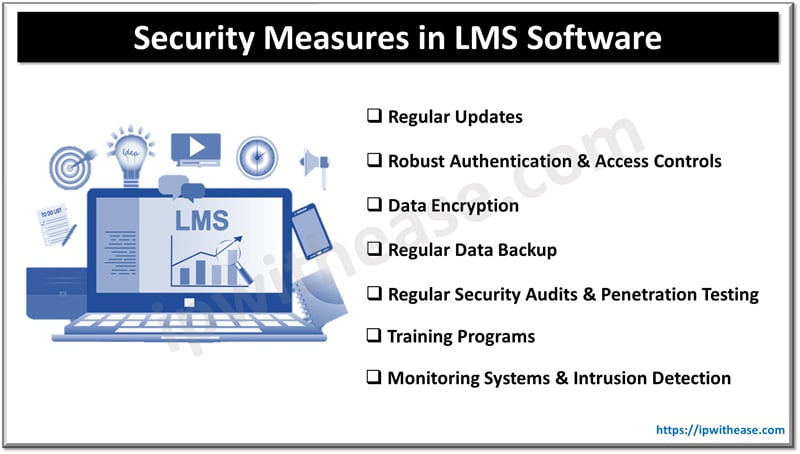
Data Encryption
Regarding safeguarding user data in LMS software, maintenance data encryption is crucial. Encryption ensures that user data remains protected when stored and transmitted. By employing encryption algorithms, institutions can effectively shield user data against threats, making it unreadable and unusable without the encryption key.
Regularly backing up data
Regularly backing up data ensures data protection in LMS software maintenance. Having recent backups readily available is vital in case of system failures or unforeseen circumstances, allowing for recovery and minimizing data loss. Institutions should establish schedules and store these backups securely to provide additional protection for user information.
Maintaining authentication and authorization mechanisms is pivotal in safeguarding user data within an LMS software environment. These mechanisms ensure authorized individuals can access the system and its functionalities, significantly reducing the entry risk. Moreover, institutions should consider implementing tools to track and monitor user activities within the system to detect any behavior.
Regular security audits & Penetration Testing
Regular security audits and penetration testing play a role in maintaining LMS software. These assessments, conducted by security professionals, help identify vulnerabilities and weaknesses before individuals can exploit them. Institutions can proactively mitigate potential security risks by performing these audits and tests.
Training programs
In addition to implementing security measures, institutions must focus on training programs and raising awareness among their staff and users. Educating users about practices in data protection—such as password security phishing awareness and safe browsing habits—can significantly reduce the risk of security breaches. Similarly, providing training to maintenance staff on security protocols during software updates and maintenance can help prevent vulnerabilities.
Monitoring systems & Intrusion detection
It is essential to have monitoring systems and intrusion detection in place to ensure accurate time threat detection and response. These systems continuously monitor network activity, server logs, user behavior, and system processes to identify any activity or unauthorized access attempts. Institutions can safeguard against data breaches and protect user information by identifying and responding to threats.
Final Words
As the reliance on LMS software grows in education and training institutions, robust security measures during software maintenance become increasingly important. Ensuring the safety of user data in LMS software requires effort.
These include implementing updates and patches using authentication and access controls, encrypting data, regularly backing up data employing secure authentication and authorization methods, conducting regular security audits and penetration testing, providing training and awareness programs, and utilizing monitoring and intrusion detection systems. Institutions must prioritize these security measures to safeguard user data and maintain trust in the system.
Continue Reading:
Cisco SD-WAN Security with Intrusion Detection and Prevention(IDS/IPS)
What is Encryption? Detailed Explanation
ABOUT THE AUTHOR
IPwithease is aimed at sharing knowledge across varied domains like Network, Security, Virtualization, Software, Wireless, etc.