Google ADs
Table of Contents
While deploying security solutions in setups, administrators may be challenged with verdict on whether to consider ACL (Access Control List) or use Firewall to secure the LAN Network setup. From a Bird’s eye view, it may seem that ACL also filter the traffic (mostly LAN and WAN communication) like Firewalls do. However, there is more to it than meets the eye – Firewalls are much more than just traffic filtering.
Key Differences between ACL and Firewall
- To start with, Firewalls perform Stateful inspection while ACLs are limited to being Stateless only. Stateful is a per-flow packet inspection, whereas Stateless (ACL) is a per-packet packet inspection. In other words, ‘state’ of flow is tracked and remembered by traditional firewall.
- In fact firewalls can also understand the TCP SYN and SYN-ACK packets which can’t be performed by ACL on Routers or Layer 3 Switches. In addition to address/port matching and connection state management, many more advanced firewalls are able to use deep packet inspection to track application-layer behaviour.
Related – Stateful and Stateless Firewall
- Firewalls can be software or hardware based. Hardware based firewalls are preferred choice when it comes to large deployments requiring dedicated appliances to address security requirements.
- Unlike Firewalls, ACLs are features on Routers and Layer 3 devices.
- Further, ACLs (Standard or extended) can perform traffic control up to Layer 4 i.e. ports and protocols while Firewalls can reach up to Layer 7 (Application Layer) of OSI model.
Watch related video for Detailed Explanation:
(Or Continue reading…)
Google ADs
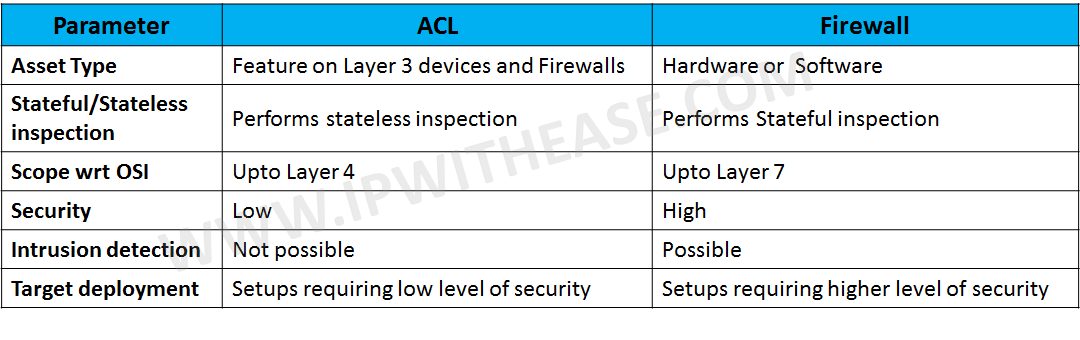
Comparison Table: ACL and Firewall
Below table illustrates difference between ACL and Firewall –
Related- Using ACL to mitigate IP Address Spoofing
ABOUT THE AUTHOR

Founder of AAR TECHNOSOLUTIONS, Rashmi is an evangelist for IT and technology. With more than 12 years in the IT ecosystem, she has been supporting multi domain functions across IT & consultancy services, in addition to Technical content making.
You can learn more about her on her linkedin profile – Rashmi Bhardwaj

Thank for informaion.
Hi from lima peru.