Table of Contents
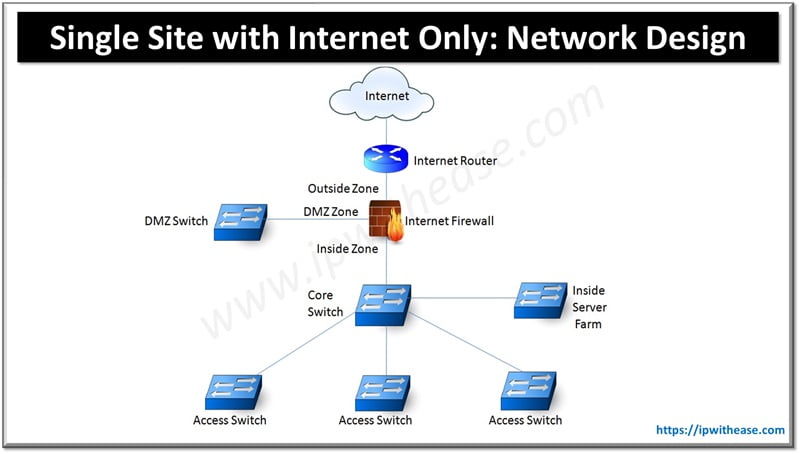
Single Site with Internet Only
Here, we will discuss a network design of single site with internet only.
Requirements:
1. Internet Access for Inside users and Servers.(Inside to Outside traffic flow)
2. Internet Access for Servers on DMZ Zone (Outside to Inside traffic flow)
3. No VPN.
Solution:
– Internet Links will terminate on Internet Router which will be Gateway for Internet traffic.
– Internet Firewall shall provide Perimeter security via separate Zones
Outside/Internet Zone (Security Level 0)
DMZ Zone (Security Level 50)
Inside Zone (Security Level 100)
Note – More on Firewall Security Zone is available here.
– Internet facing portals may be placed on DMZ Switch (e.g. Web Server, Public DNS Server etc.).
– Core Switch will in secured inside Zone of Internet Firewall will form the layer 3 gateway for all the VLANs namely –
User VLANs, Inside Server VLANs, Management VLAN etc. It would be preferred to make Core Switch as gateway to all the Users/Server VLANs in Inside Zone and not the Internet Firewall. This practice offloads the firewall from Layer2 broadcast and ARP queries from Inside Zone User and Server VLANs endpoints.
– User Access switches and Server farm switches will connect directly to end hosts.
Related- DMZ Cisco ASA Configuration
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj