Table of Contents
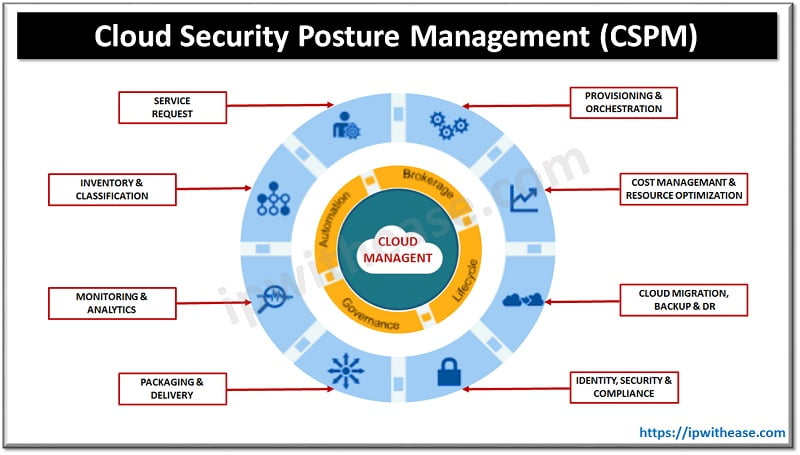
Introduction to CSPM
In the cyber community industry we define “Cloud Security Posture Management”, commonly named as CSPM, a class of security tools that have been initially defined by Gartner. This kind of security tools include cases for monitoring compliance, integrate DevOps, incidents response and risk assessment and visualization.
The initial name for Cloud Security Posture Management was Cloud Infrastructure Security Posture Assessment and was defined to configure public cloud IaaS and PaaS services in organizations and companies that needed to address cloud risks. Gartner advices IT Managers to invest in “Cloud Security Posture Management” CSPM processes and tools, in order to avoid misconfigurations that can lead to data leakage in the future.
Top Cloud Security Posture Management (CSPM) Solutions
Due to the fact that cloud security threats are increasing rapidly, this has resulted in increased need for CSPM services. The top 5 CSPM solutions that are changing cloud security landscape are defined below:

Zscaler
Zscaler technology initially started providing services as a secure web gateway provider. Later on, they enriched the services by adding next-generation firewall and zero-trust network access. In the CSPM industry, Zscaler is a leader due to the fact that it collects actual configurations from cloud service providers. Further, the results are compared against cloud security best practices. Finally risks are analyzed and misconfigurations are fixed.
Orca Security
Orca Security is a startup company, founded last year by Check Point. The main services that distinguishes its strategy from the competition, is the combination of CSPM and cloud workload protection platform (CWPP) capabilities into a single platform. By creating this platform, Orca provides deep visualization and analysis across cloud environments, without the complexity and huge time resources to deploy. Furthermore, Orca started selling this cloud security platform since last August and also supports AWS, Azure, and Google Cloud services.
Aqua Security
One hot news in IT industry reveals that CloudSploit was purchased by Aqua Security last November. This business action gave Aqua Security the advantage to provide CSPM services in the industry. They now utilize CloudSploit’s SaaS platform across the customer portfolios. The main advantage in this platform is the automatic management of cloud security risks and resource estates. Furthermore, Aqua Security updated it’s CSPM platform in April to include features such as Aqua Dynamic Threat Analysis.
Sophos Security
Sophos, a network endpoint security vendor, bought Avid Secure to increase its cloud security services. Avid Secure used to provide report analysis and automation for governance, risk and compliance. They used software mainly in AWS, Azure and GCP Cloud platforms. Nowadays Sophos Security gained Avid’s customer portfolio and offers extended services in CSPM industry.
Trend Micro
rend Micro invested 70 Million $ on cloud conformity last year to improve misconfigurations in the public cloud. This CSPM acquisition was the initial for Trend Micro since November 2017, when Immunio was bought as a web application vendor. The benefits nowadays are a sophisticated platform that maintains security, governance and compliance in the public cloud. This services are also enchanted by technologies using AWS and Azure Cloud.
Conclusion
Cloud Security Posture Management can be a powerful tool for cloud security based operations, such as complex environments that combine many types of cloud technologies, multivendor support, and hybrid network elements. CSPM should be carefully implemented because of the especially crucial for mutable infrastructure and DevOps pipelines. They intend to be inherently complex.
An expert’s assessment of this situation is essential and policies should be addressed to meet customer’s needs. Then finding the optimal solution that complies with Company’s policies is an easy task. CSPM implementations, according to Gartner research, can reduce cloud security misconfiguration by up to 80%. Such kind of companies that offer CSPM services, described in the article can also reduce the possibilities that your systems are breached by cyber attackers. Therefore CSPM solutions have to be integrated into development processes, enabling a better build security into your applications and deployments.
ABOUT THE AUTHOR

You can learn more about her on her linkedin profile – Rashmi Bhardwaj